![[Studying] Analyzing Poison Ivy](/images/meme/natsu_cake.jpg)
![[Learning] How to Manually Unpack UPX and ASPack](/images/meme/mika_love.png)
[Learning] How to Manually Unpack UPX and ASPack
READ MORE +![[Reverse Engineering] How I Found a Suspicious Redistribution of My Project](/images/meme/nagusa_crying.jpg)
[Reverse Engineering] How I Found a Suspicious Redistribution of My Project
READ MORE +![[Studying] Analyzing ProRat](/images/meme/mika_XD.png)
[Studying] Analyzing ProRat
READ MORE +![[Learning] How to Configure the Network of Your Virtual Machine using VMware Workstation](/images/meme/koyuki_crying.gif)
[Learning] How to Configure the Network of Your Virtual Machine using VMware Workstation
READ MORE +![[Troubleshooting] Installing VMware Tools on Windows XP and Windows 95 with VMware WorkStation 17](/images/meme/mika_rollcake_hit.png)
[Troubleshooting] Installing VMware Tools on Windows XP and Windows 95 with VMware WorkStation 17
READ MORE +![[Learning] How to Setup Your Experimental Environment for Malware Analysis](/images/meme/himari_coffee.2.jpg)
[Learning] How to Setup Your Experimental Environment for Malware Analysis
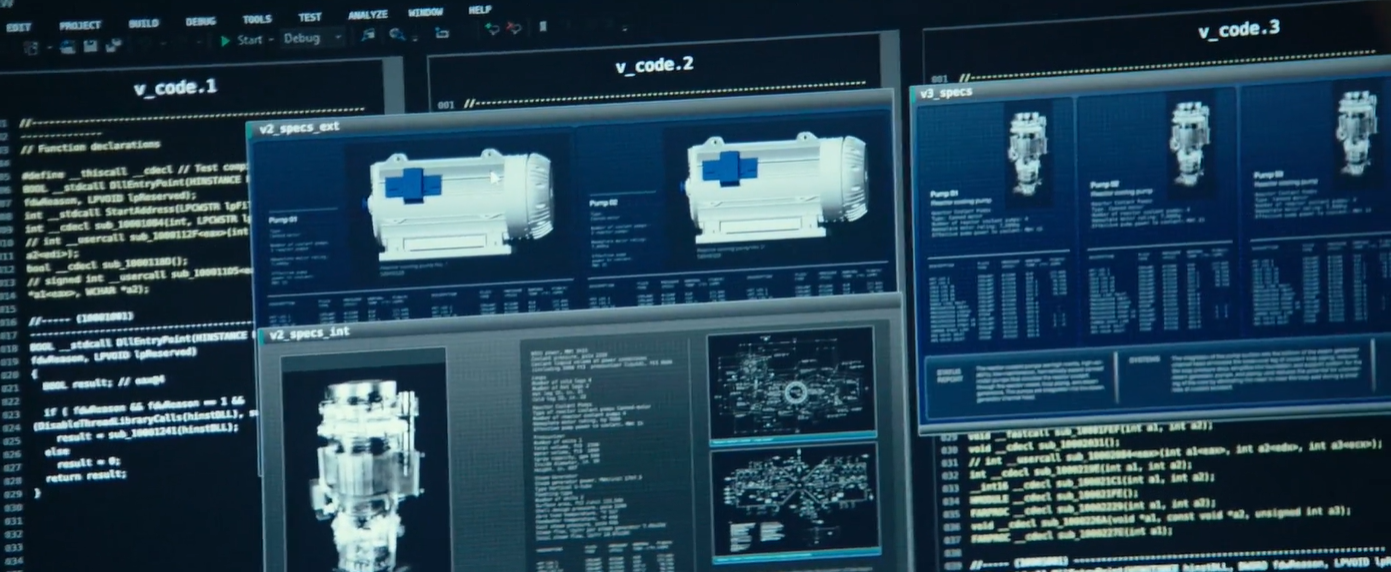
READ MORE +![[Studying] Analyzing BeastDoor](/images/meme/rio_pc.jpg)
[Studying] Analyzing BeastDoor
READ MORE +![[Studying] Analyzing Sub7 (SubSeven)](/images/meme/nagisa_neko.png)
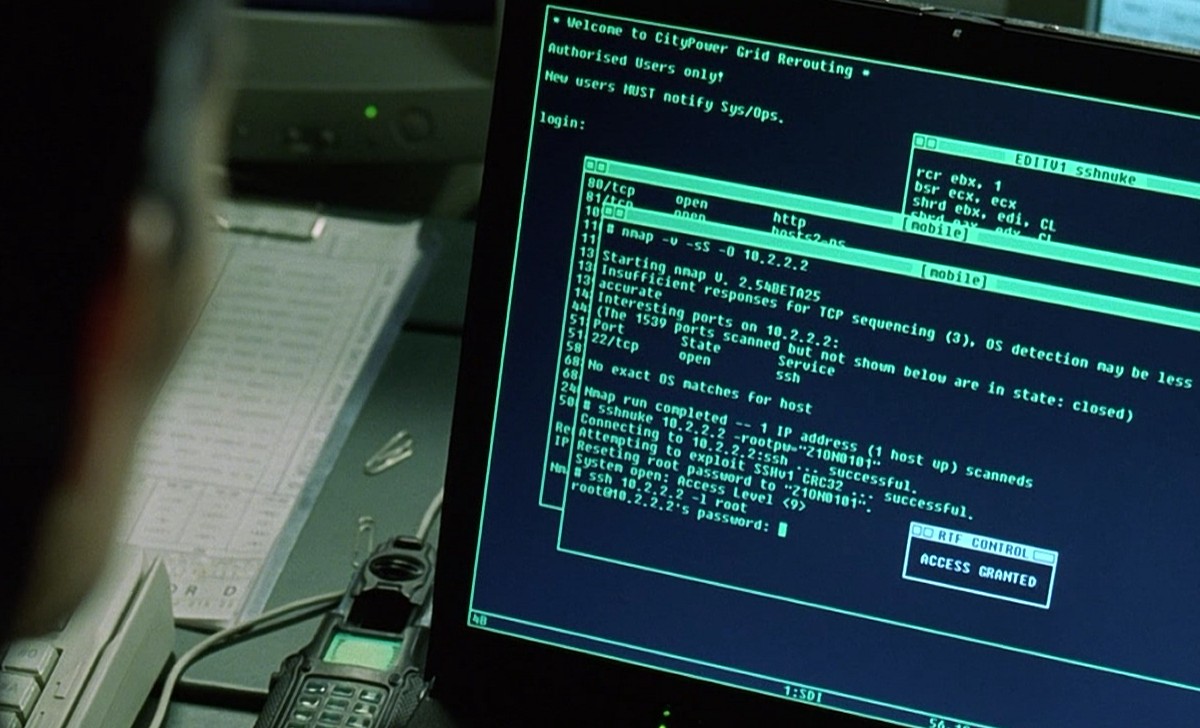
[Studying] Analyzing Sub7 (SubSeven)
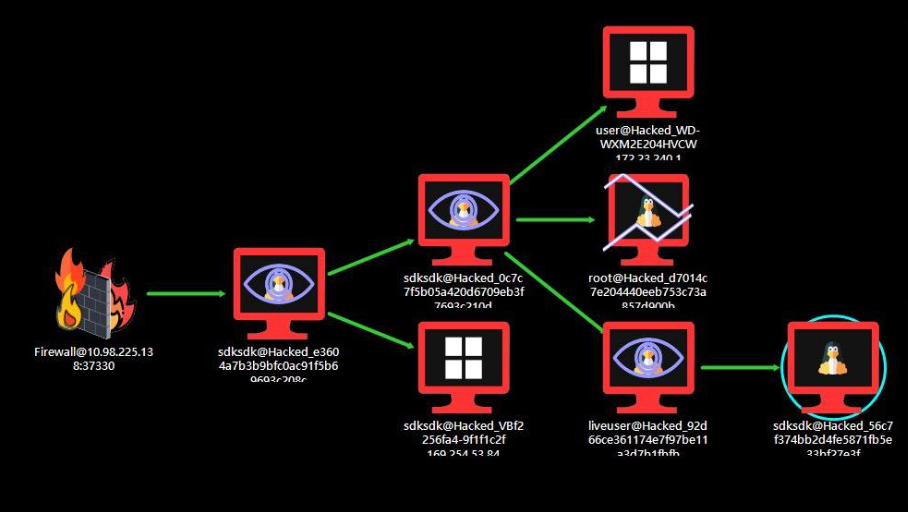
READ MORE +![[Studying] Analyzing Back Orifice](/images/meme/mika_cute.jpg)