[Studying] Analyzing Other Variants of the njRAT Family
Last Update:
Word Count:
Read Time:
The last article of the njRAT family…maybe?
Introduction
This article is part of my series: Inside Different Generations of RATs and part of the njRAT Family.
If you are interested in the full series, please refer to the linked pages above.
This article presents an analysis of several similar variants of the njRAT Family.
Observations
From these variants, it can be observed that most modifications fall into the following categories:
- Cosmetic changes (e.g., GUI redesign)
- Feature reuse across variants
- Minor functional extensions
This suggests that many variants are not fundamentally new malware, but rather iterative modifications built on existing codebases.

Other njRAT Versions and Variants
As introduced in the previous article, I analyzed several Korean variants. This article also serves to document other versions and variants of the njRAT Family.
In my opinion, it is not meaningful to write separate articles for minor variations between these variants.
Compared to the previous analysis articles, this article does not introduce significant new reverse engineering insights. I decided to write this article to complete the overall landscape of the njRAT Family.
Experimental Environment
To safely conduct malware analysis, the environment should be isolated using virtual machines. Under no circumstances should malware be executed on a personal or production system.
| Tool | Description |
|---|---|
| ExeInfo PE | Detect packers, compilers, and basic file metadata |
| Detect It Easy (DIE) | Identify packers, protectors, and signatures |
| Wireshark | Network traffic analysis |
| de4dot | .NET de-obfuscator |
| .NET Reactor Slayer | .NET Reactor de-obfuscator |
| dnSpy | .NET reverse engineering and debugging |
| pestudio | Static PE analysis tool |
| Device | IP Address | Description |
|---|---|---|
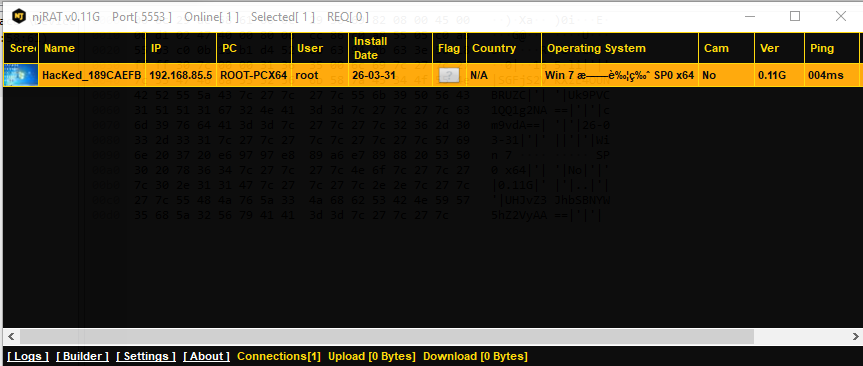
| Windows 7 x64 (VM) | 192.168.85.5 | Victim machine |
| Windows 10 x64 (VM) | 192.168.85.3 | Analysis machine |
The two virtual machines were configured within an isolated internal network to prevent unintended external communication. If you want to know how to set up your experimental environment, please view:
- How to Setup Your Experimental Environment for Malware Analysis
- Installing VMware Tools on Windows XP and Windows 95 with VMware WorkStation 17
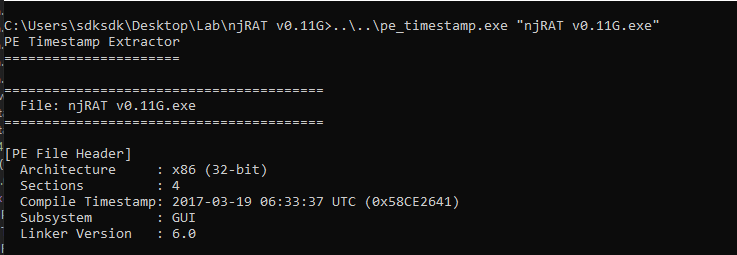
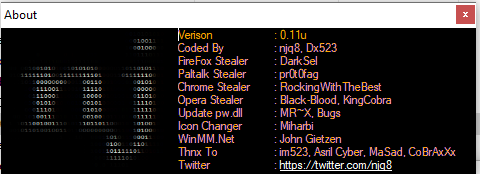
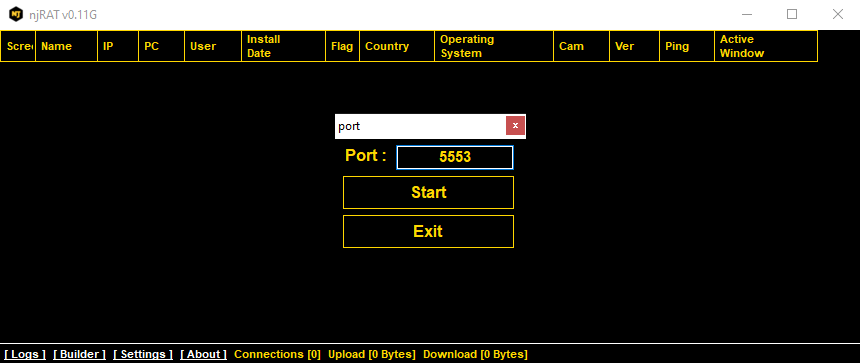
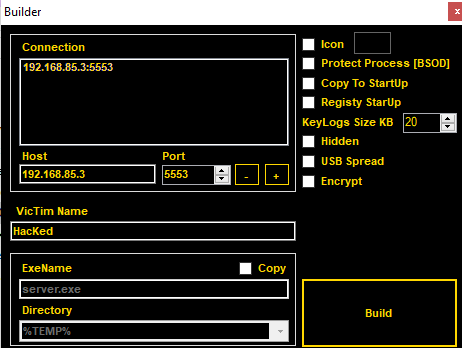
njRAT v0.11
This version was developed by the original author njq8 of njRAT v0.7.
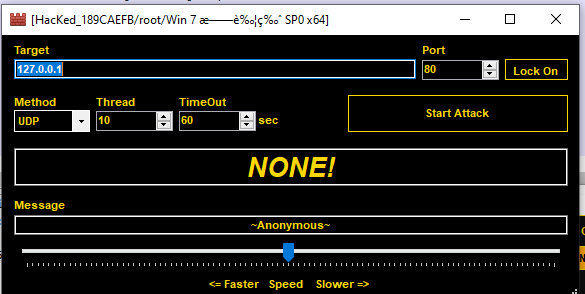
Stress Test and Pastime
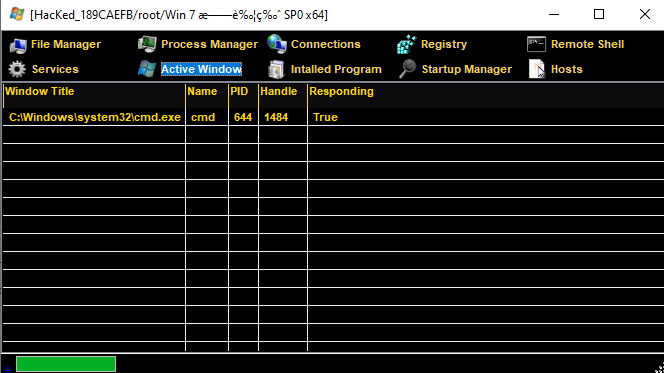
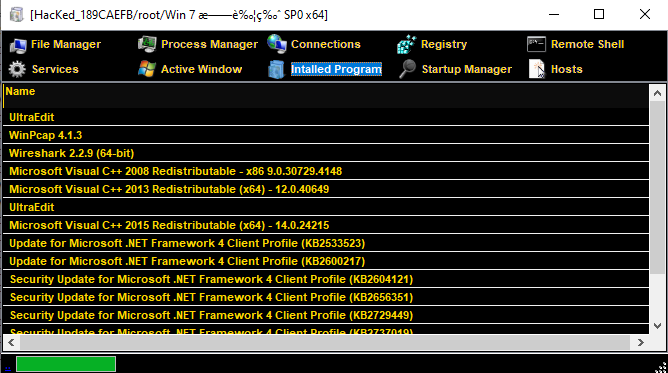
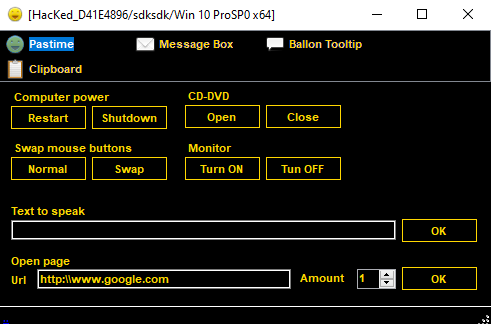
Compared to the previous versions, the author added new features such as Stress Test and Pastime (Fun stuff):
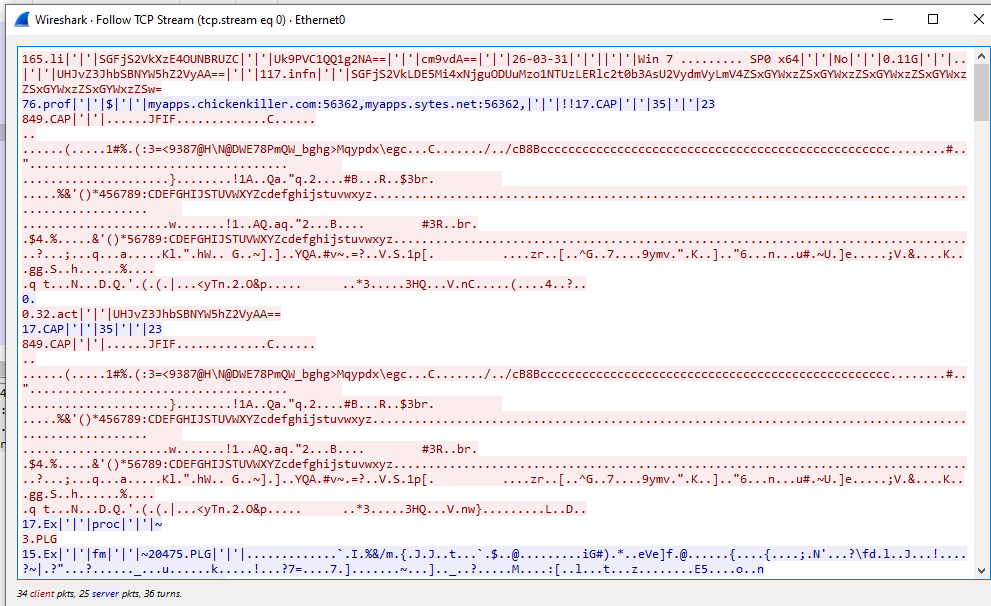
Protocol
Other Variants
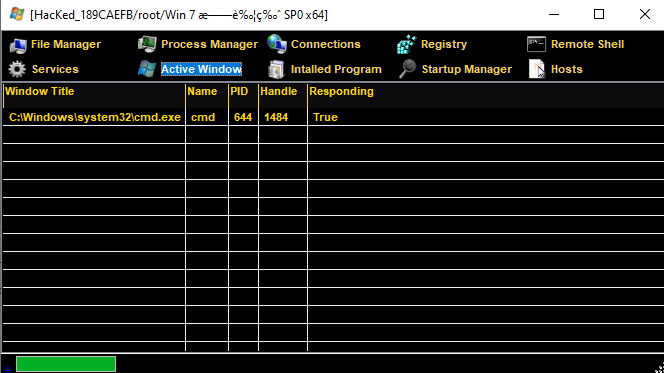
Here, I also want to show several variants and provide a brief overview.
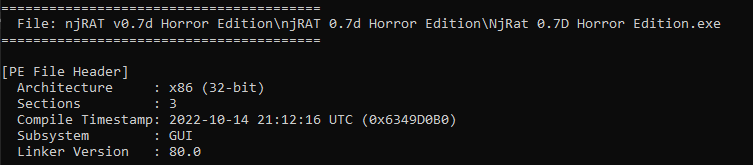
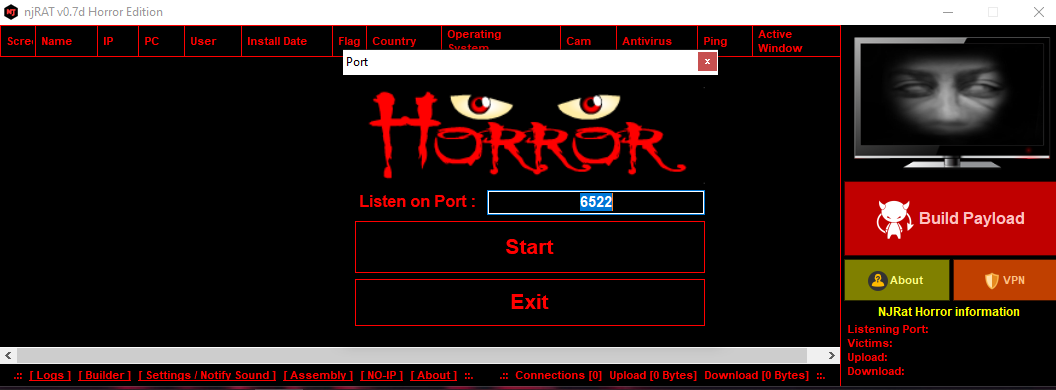
Horror Edition
The biggest change in this variant is it provides a horror-themed graphical user interface (e.g., scenes from horror movies)
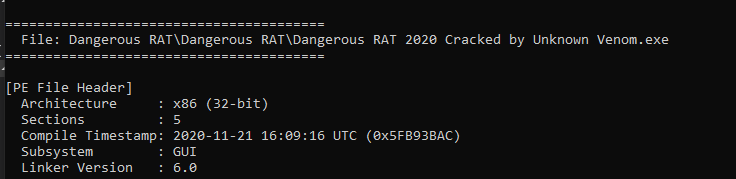
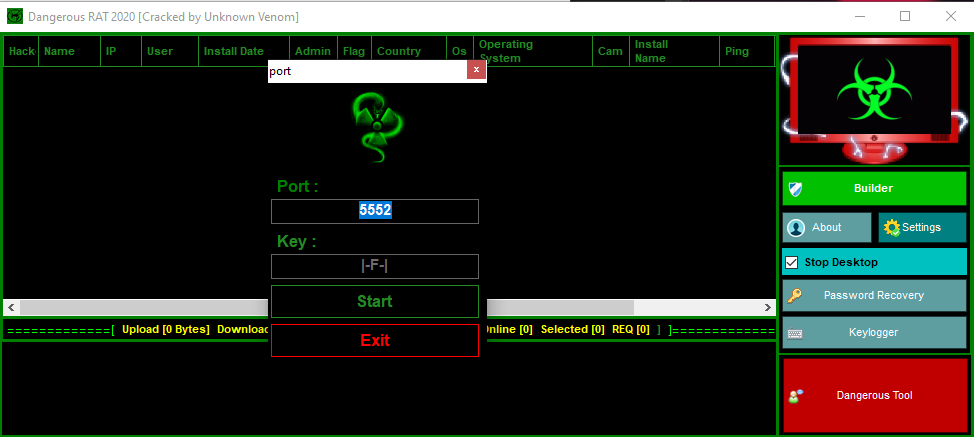
Dangerous RAT
This variant was likely released by the same author of the Danger Edition. It appears to incorporate several features from njRAT Danger Edition 2018:
Conclusion
This article presents a high-level overview of several variants within the njRAT Family. In addition, it is probably the last article of the njRAT Family analysis.
Although these variants introduce minor differences, most of them share the same core architecture and functionality derived from earlier versions such as njRAT v0.7.
This highlights a common pattern in malware evolution, where new variants are often created through incremental modifications rather than entirely new designs.
If you have any comments or suggestions, please feel free to leave them below!
THANKS FOR READING
