[Studying] Analyzing DarkComet
Last Update:
Word Count:
Read Time:
Introduction
DarkComet is one of the most well-known remote access trojans (RATs) widely used during the late 2000s and early 2010s. Despite being originally developed as a remote administration tool, it was later abused by threat actors to gain unauthorized access to victim systems.
In this article, I analyze the DarkComet payload through static analysis and reverse engineering. The goal is to understand how the malware establishes command-and-control (C2) communication and how its core functionalities are implemented internally.
This article is part of my series Inside Different Generations of RATs, where I study the evolution of RAT malware by reversing different families from various time periods. If you are interested in the full series, please refer to the article linked above.

DarkComet
DarkComet is a remote access trojan (RAT) developed by Jean-Pierre Lesueur (known as DarkCoderSc), an independent programmer and computer security coder from France. Although the RAT was originally developed back in 2008, it began to proliferate in early 2012. DarkComet was later discontinued, partly due to its use during the Syrian civil war to monitor activists and also due because the author feared potential legal consequences for undisclosed reasons 1.
Different versions of DarkComet can still be found on the internet.
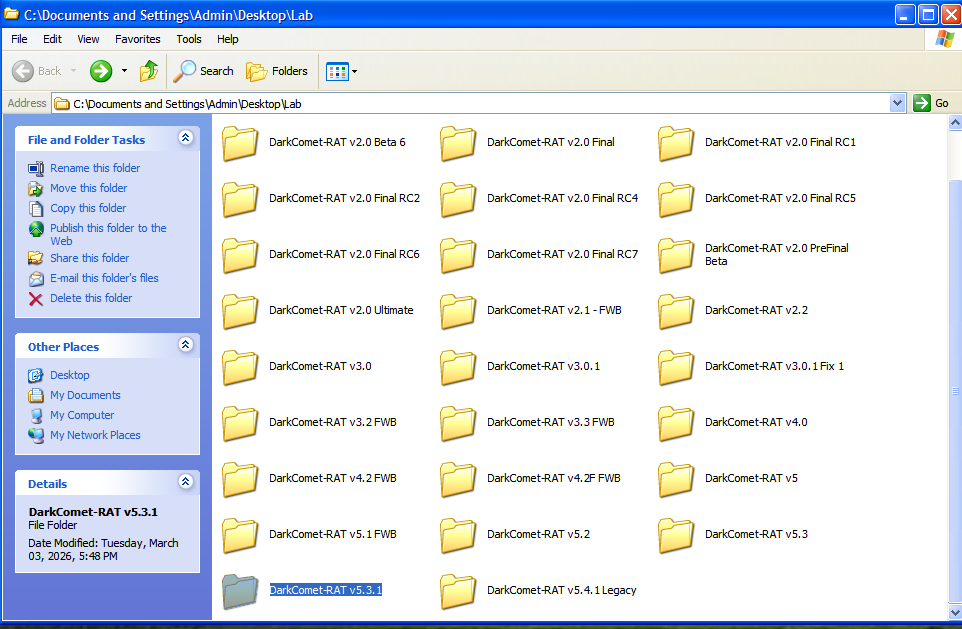
This article mainly discusses version 5.3.1.
Experimental Environment Setup
To safely conduct malware analysis, the environment should be isolated using virtual machines. Under no circumstances should malware be executed on a personal or production system.
| Tool | Description |
|---|---|
| ExeInfo PE | Executable analysis tool used to detect packers, compilers, and basic file properties |
| Detect It Easy (DIE) | File identification tool used to detect packers, protectors, and compiler signatures |
| UPX | Open-source executable packer used to compress and decompress binaries |
| Wireshark | Network protocol analyzer used to capture and inspect live or recorded traffic |
| Ghidra | Open-source software reverse engineering framework developed by the NSA |
| Device | IP Address | Description |
|---|---|---|
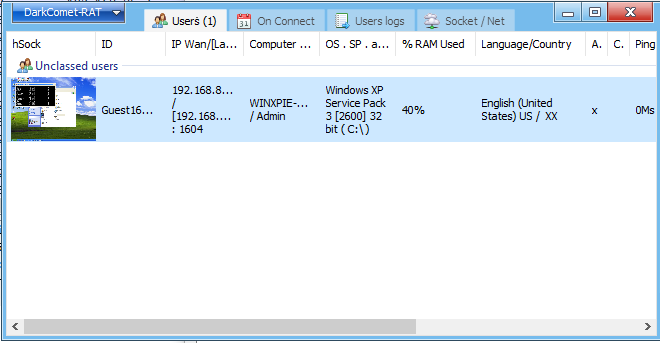
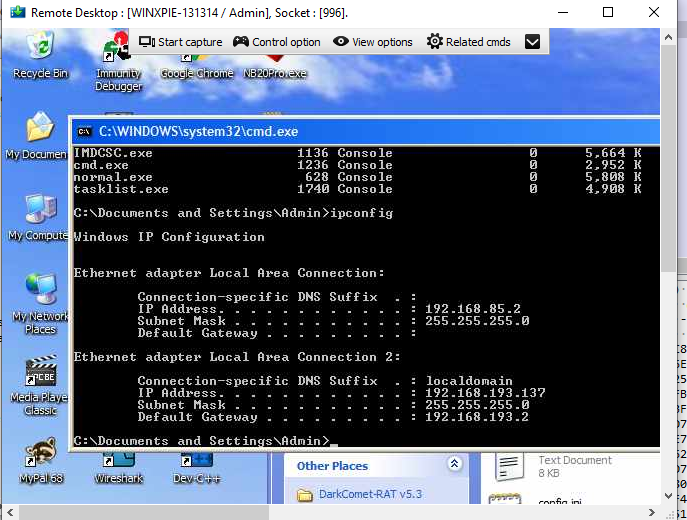
| Windows XP x86 (VM) | 192.168.85.2 | Victim machine used for executing both the controller and payload |
| Windows 10 x64 (VM) | 192.168.85.3 | Analysis machine used for reverse engineering |
The two virtual machines were configured within an isolated internal network to prevent unintended external communication. If you want to know how to set up your experimental environment, please view:
- How to Setup Your Experimental Environment for Malware Analysis
- Installing VMware Tools on Windows XP and Windows 95 with VMware WorkStation 17
Usage
Launch DarkComet.exe.
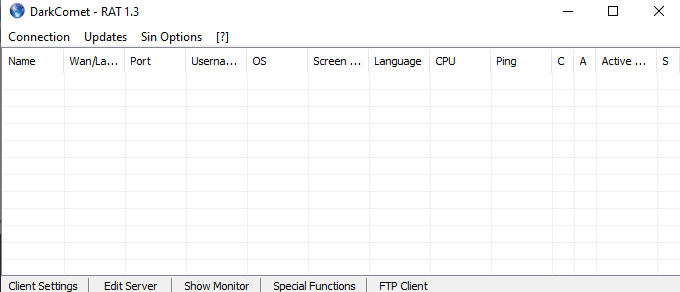
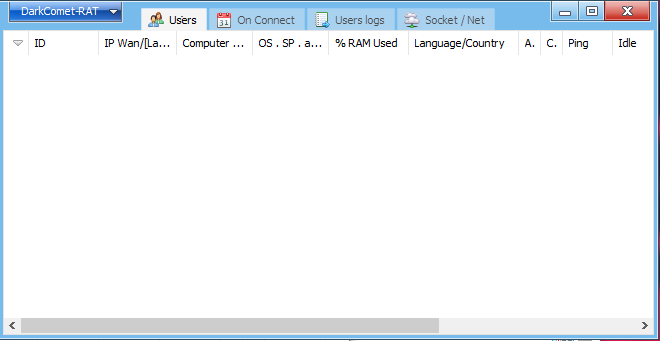
DarkComet provides two panels for configuring the payload (server stub):
Here, the term “server” might be confusing from a modern perspective. Compared to the previous articles, this GUI application acts as the server in the network architecture, while the payload is the client. However, in that era, the term server often referred to the service provider—the payload—which provides the remote control capabilities.
To avoid confusion, this article uses the following terms:
- Controller: attacker-side application
- Payload: executable deployed on the victim machines
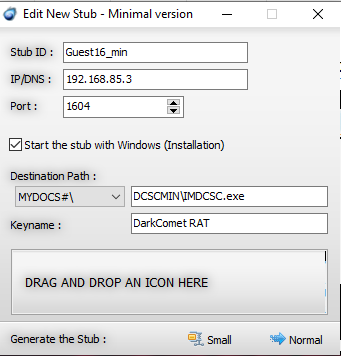
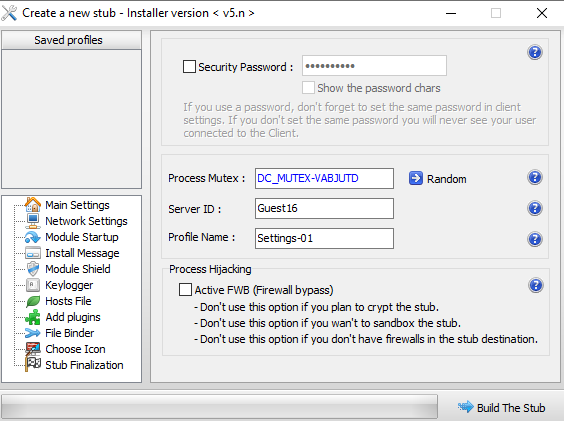
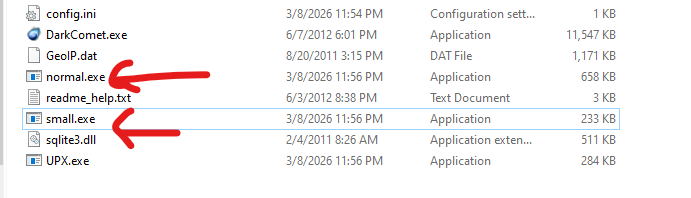
The minimal version builder allows the users create a “small” payload or “normal” payload. I will discuss the difference in the reverse engineering section. In this article, I refer to them as small.exe and normal.exe, respectively.
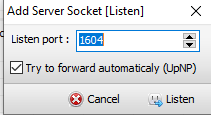
DarkComet is capable of binding multiple ports to establish TCP communication channels:
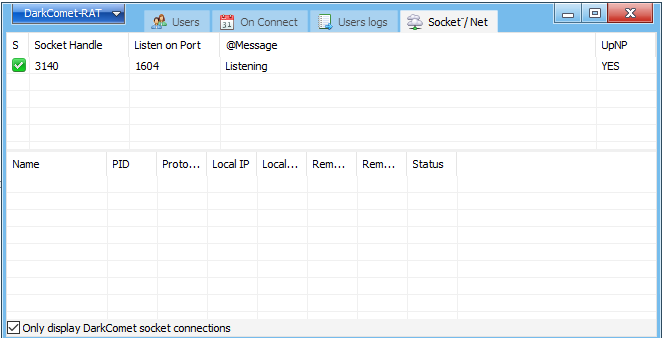
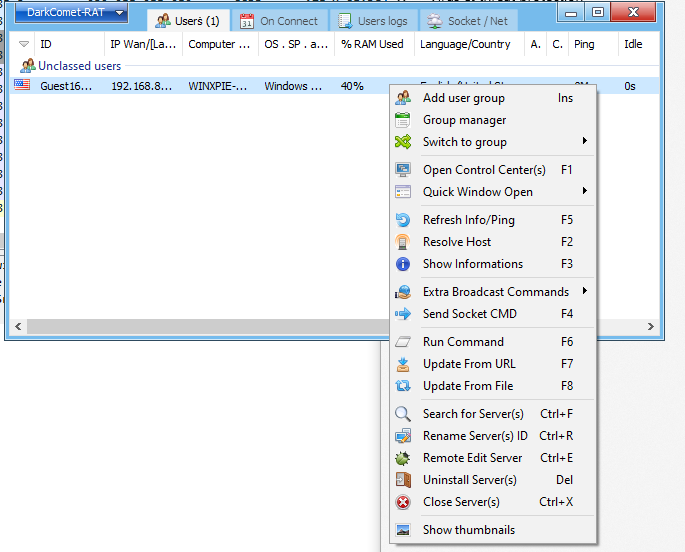
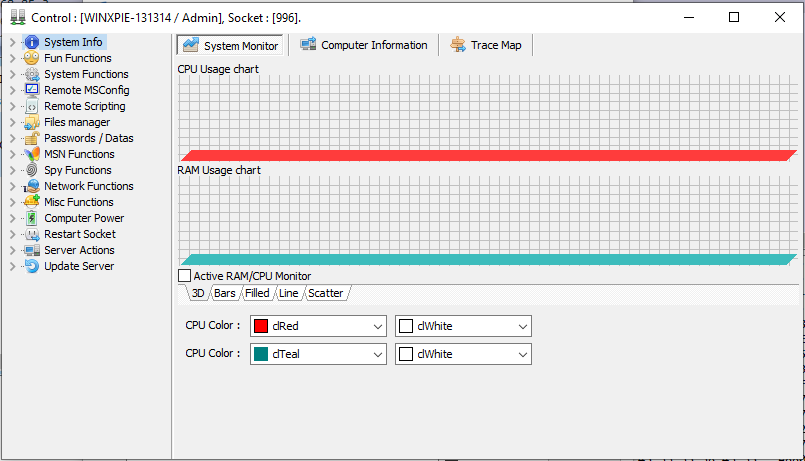
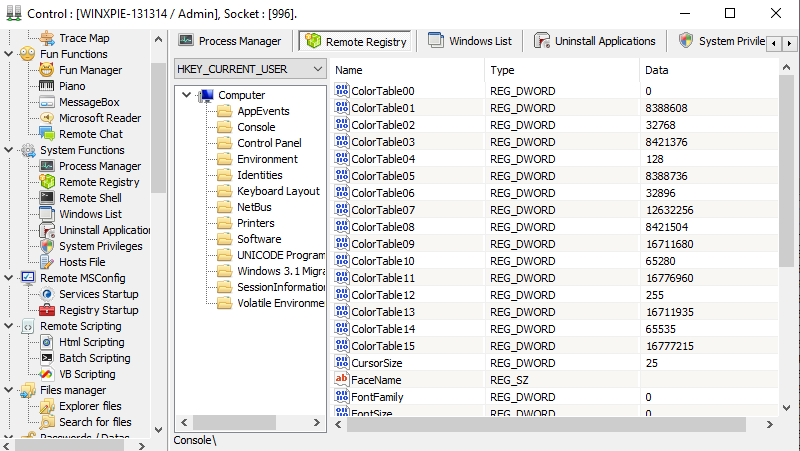
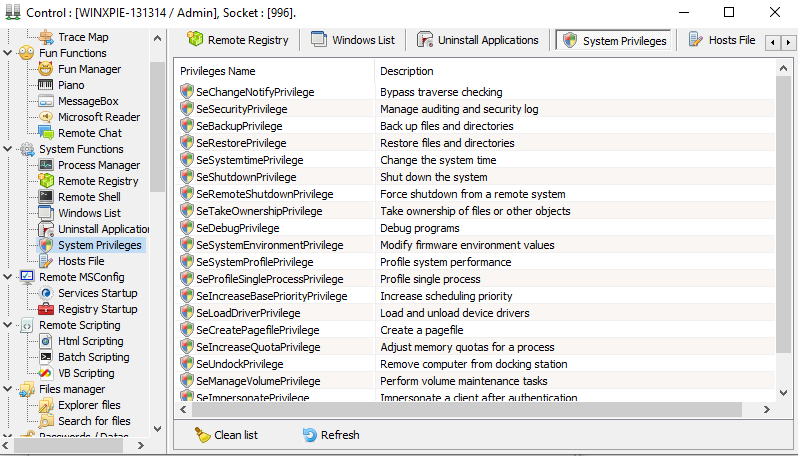
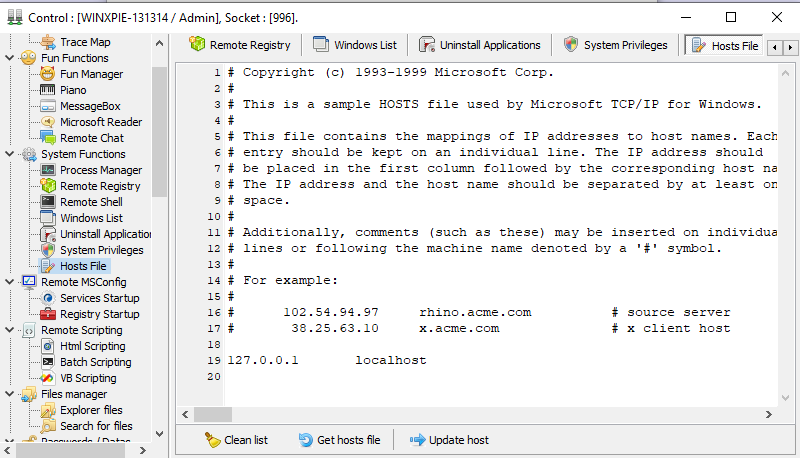
Once the target machine is compromised, the controller can control the remote machine using multiple functionalities:
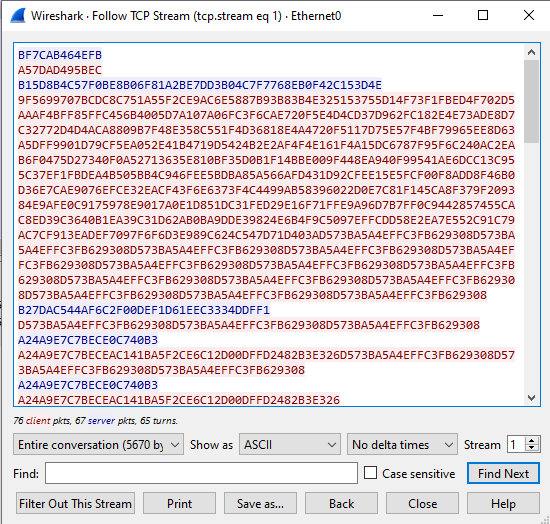
Protocol Analysis
The communication channel is protected using RC4 algorithm. I will demonstrate it in reverse engineering section:
Reverse Engineering
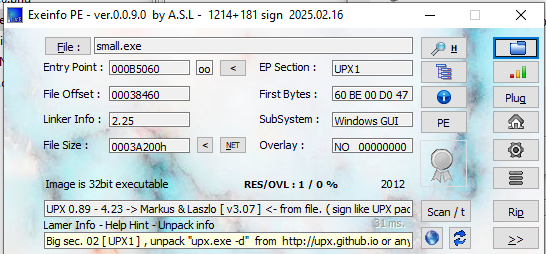
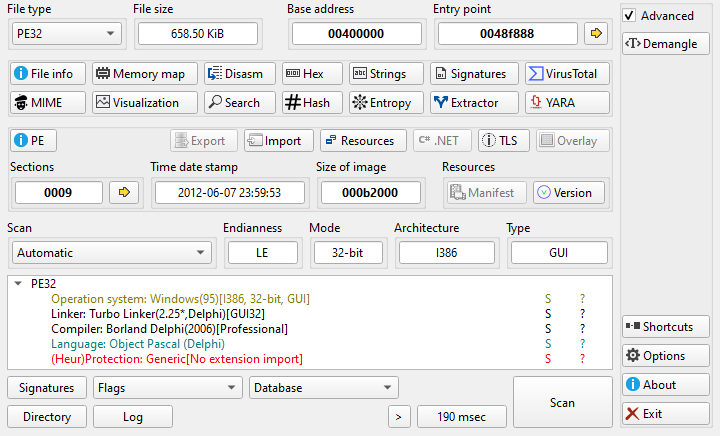
Open the payload executables with ExeInfo and DIE (Detect It Easy):
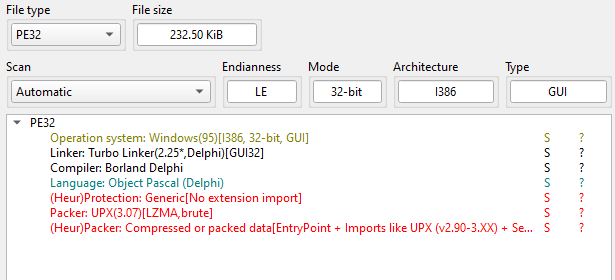
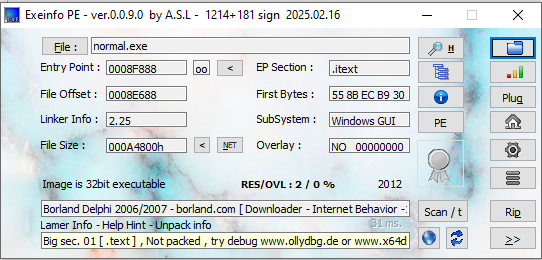
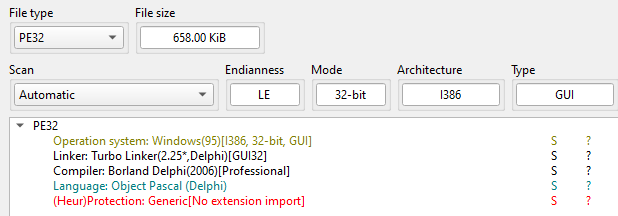
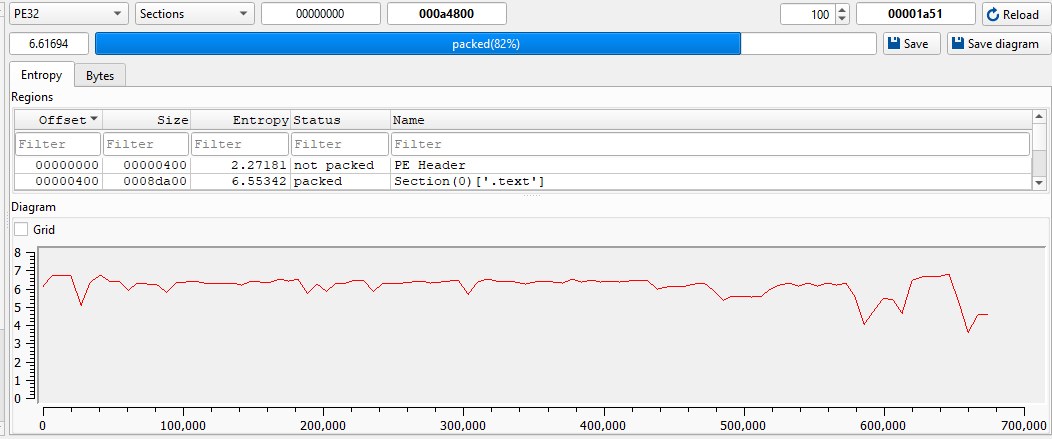
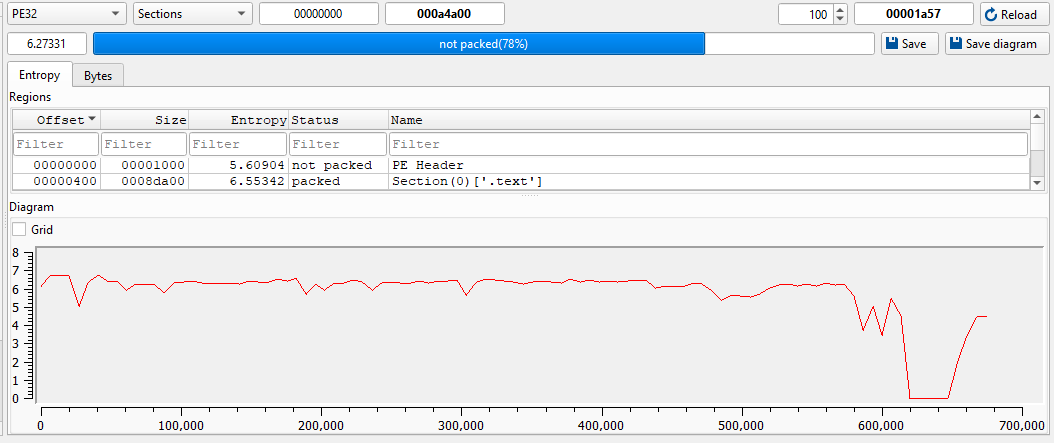
normal.exe appears to be unpacked. However, it has relatively high entropy:
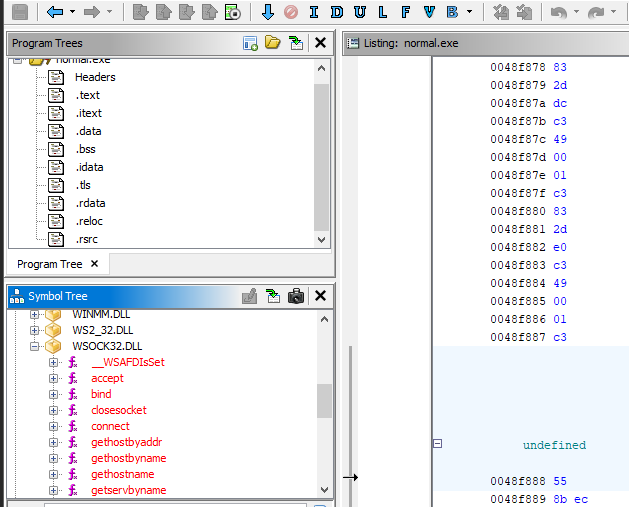
Nevertheless, Ghidra can still correctly display the imported modules. It seems like Delphi compiler leds high entropy. This is expected because compilers such as Visual Studio C++ or Delphi often add stubs or perform optimizations when generating executables.
Therefore, in this case, only small.exe is packed. We can unpack it manually or by using upx.exe. If you are interested in manual unpacking UPX, please refer to this article.
Using upx.exe:1
upx.exe -d small.exe -o unpacked_small.exe
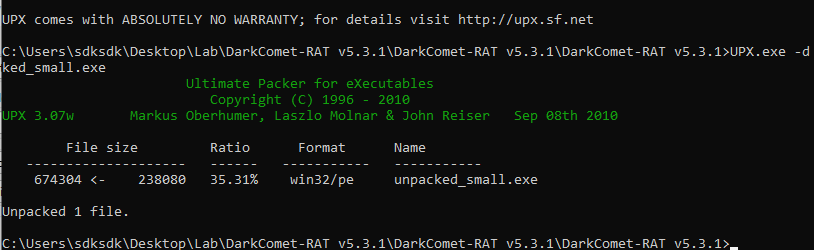
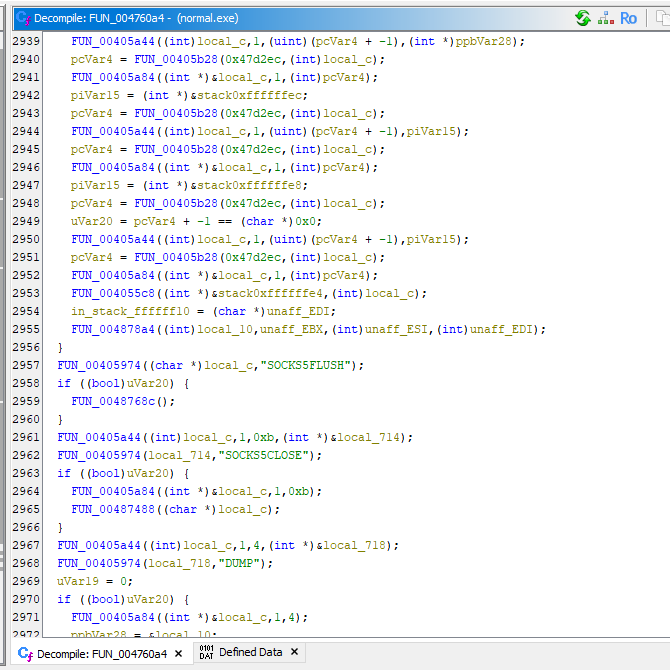
Next, we can perform reverse engineering on both normal.exe, unpacked.exe. After further investigation, I realized that these two executables are actually identical.
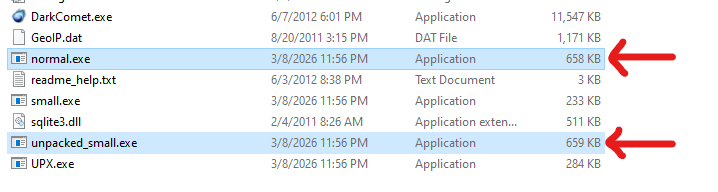
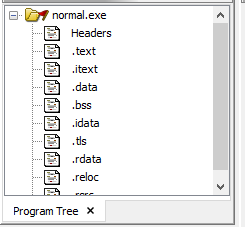
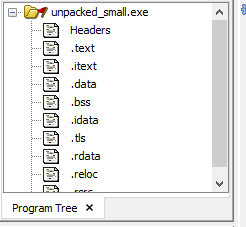
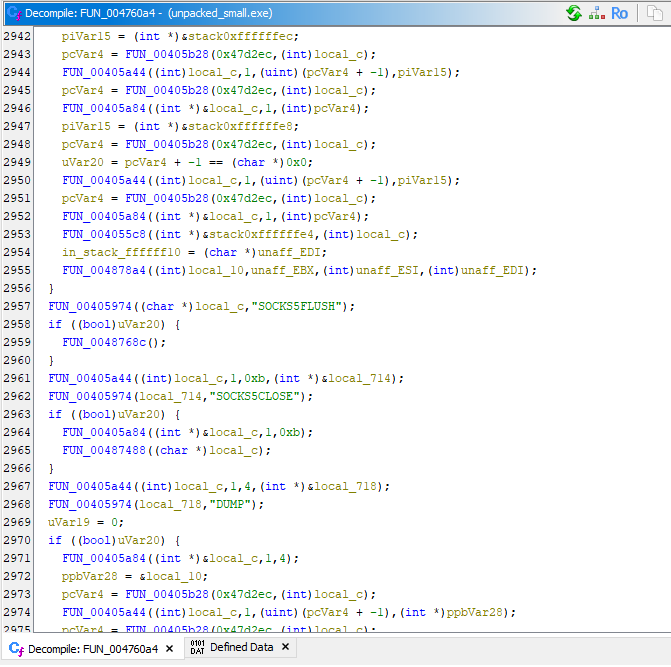
Initially, I thought small.exe might be a stage-1 payload that downloads or loads a stage-2 payload from the C2 server. However, it turns out that it is simply called “small” because it is packed with UPX. Therefore, the reverse engineering analysis in this article focuses on normal.exe.
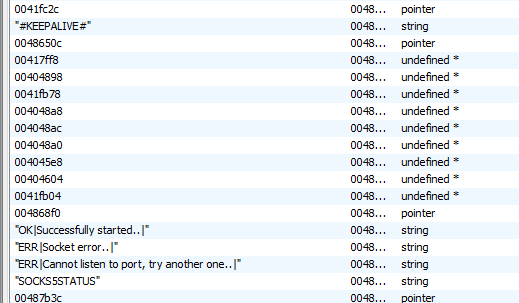
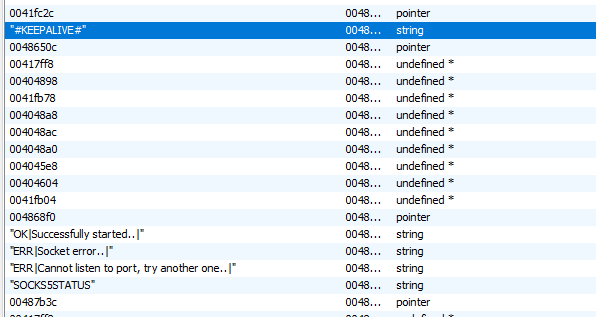
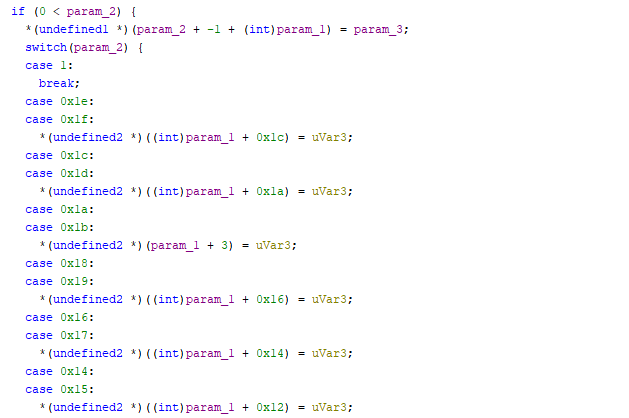
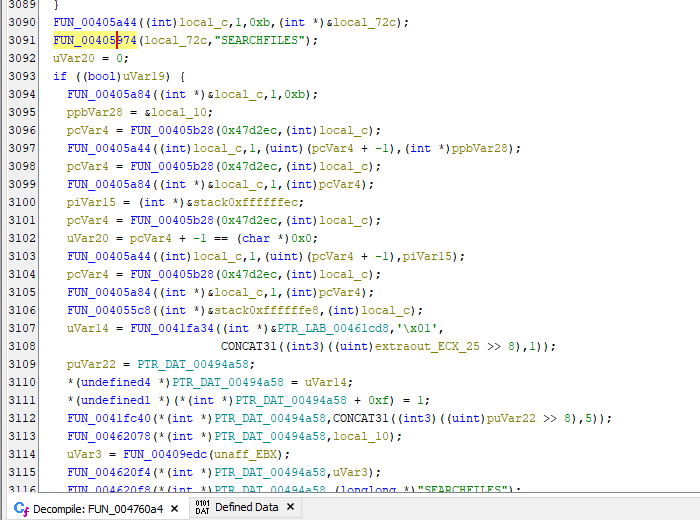
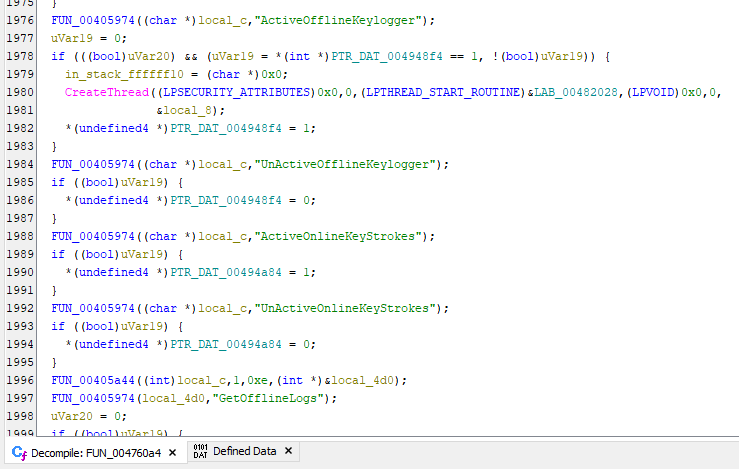
Notice that DarkComet uses different integer and string values to identify C2 commands:
The communication is protected using the following function:
1 | |
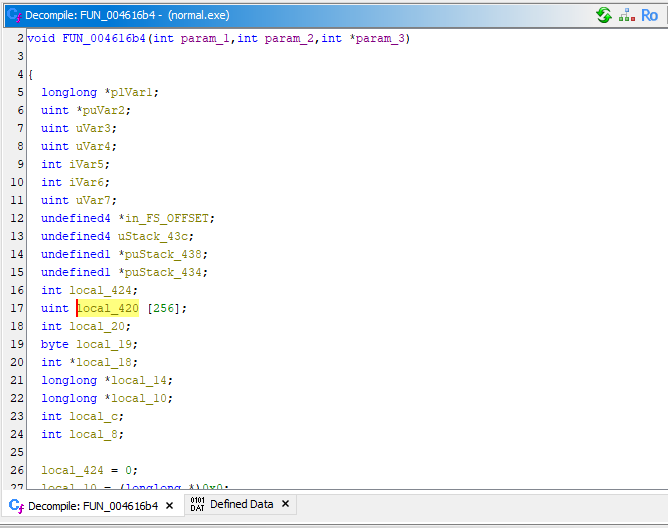
256 bytes S-box:1
uint local_420[256]
Key Scheduling Algorithm (KSA):1
2
3
4
5
6
7uVar4 = 0;
puVar2 = local_420;
do {
*puVar2 = uVar4;
uVar4 = uVar4 + 1;
puVar2 = puVar2 + 1;
} while (uVar4 != 0x100);
Pseudo Random Generation Algorithm (PRGA):1
2
3
4
5
6
7
8
9
10uVar3 = uVar3 + 1 & 0xff;
uVar7 = uVar7 + local_420[uVar3] & 0xff;
swap(S[i], S[j]);
uVar4 = S[i] + S[j] & 0xff;
byte = S[uVar4];
data[i] ^= byte;
Therefore, we can rewrite the decompiled code with the following pseudo code:1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33function RC4_EncryptDecrypt(data, key):
key_len = length(key)
data_len = length(data)
S = array[256]
//S-box
for i from 0 to 255:
S[i] = i
//KSA
j = 0
for i from 0 to 255:
j = (j + S[i] + key[i mod key_len]) mod 256
swap(S[i], S[j])
//PRGA
i = 0
j = 0
for k from 0 to data_len-1:
i = (i + 1) mod 256
j = (j + S[i]) mod 256
swap(S[i], S[j])
t = (S[i] + S[j]) mod 256
keystream = S[t]
data[k] = data[k] XOR keystream
return data
Conclusion
This article presented a reverse engineering analysis of the infamous RAT DarkComet. It provides multiple advanced features that allow attackers to gain full control over compromised Windows XP systems.
From the 2000s to the early 2010s, many RATs adopted the RC4 algorithm to protect their communication channels.
References
1. https://en.wikipedia.org/wiki/DarkComet ↩
THANKS FOR READING
